Cbw
Stay compliant under the Cybersecurity Act
Safeguard critical applications, strengthen resilience, and get audit-ready proof of compliance with Codekeeper’s software escrow solutions.

By late 2025, the Cybersecurity Act will be enforced. If you can’t demonstrate supply chain security and continuity, you’ll pay with penalties, lost contracts, and public scrutiny.
The Cybersecurity Act: What you need to know
What is the Cybersecurity Act?
The Cybersecurity Act — officially the Cyberbeveiligingswet (Cbw) — is the Netherlands’ version of the EU’s NIS2 directive. It introduces stricter rules for risk management, incident reporting, and resilience to protect critical services from rising cyber threats.
Who needs to comply with the Cybersecurity Act?
Under the Cybersecurity Act (Cbw), all NIS2-designated “essential” and “important” entities in the Netherlands must comply with strict new cybersecurity rules. This includes:
Energy
Essential entity
Transport
Essential entity
Finance
Essential entity
Healthcare
Essential entity
Digital infrastructure
Essential entity
Water supply
Essential entity
ICT-service management
Essential entity
Public administration
Essential entity
Space
Essential entity
Postal services
Important entity
Waste management
Important entity
Chemicals
Important entity
Food
Important entity
Manufacturing
Important entity
Digital providers
Important entity
Research
Important entity
Around 10,000 Dutch organizations fall under the Cbw, but even smaller suppliers may be indirectly impacted through contractual requirements from regulated partners.
Key Cybersecurity Act requirements
The Cybersecurity Act (Cbw) requires essential and important entities to meet seven fundamental obligations:
1
Risk and continuity management
Run risk analyses, set incident response, and maintain continuity and recovery plans.
2
Operational security
Protect networks, enforce cyber hygiene, and secure data with encryption.
3
Identity and access control
Use role-based access, secure asset management, and require MFA for critical systems.
4
Supply chain security
Assess suppliers, strengthen contracts, and reduce third-party risks.
5
Governance and testing
Audit and test security controls to prove effectiveness and compliance.
6
Registration duty
Register in the national Cbw entity list for visibility and EU coordination.
7
Incident reporting
Report major cyber incidents quickly to sector supervisors and the NCSC.
The software escrow — Cybersecurity Act connection
Software escrow creates a direct pathway to Cbw compliance by strengthening supply chain resilience, proving recovery capabilities, and demonstrating that continuity plans actually work.
Cbw risk
Critical software suppliers suddenly fail or go bankrupt
Loss of access to source code needed for updates and fixes
Inability to recover from vendor-related cyber incidents
Management held personally liable for third-party failures
Software escrow solution
Stores code, data, and documentation in a secure vault
Ensures operational recovery when vendors can’t deliver
Demonstrates continuity and resilience in regulator audits
Automates deposits to keep compliance always up to date
Compliance outcome
Cbw’s supply chain security obligations satisfied
Reduced exposure to cascading third-party disruptions
Verified recovery and continuity evidence for audits
Protection from multi-million Euro fines and sanctions
With software escrow in place, your organization gains verifiable control over critical software assets. That means you can show regulators — and your board — that even if suppliers fail, your essential services will keep running.
Let us help you be Cybersecurity Act compliant
The Cbw introduces new obligations and new risks. At Codekeeper, we’ve already guided thousands of organizations through complex regulations, and we know the road ahead for you.
We see the challenges you face:
Meeting Cbw obligations under tight deadlines
Management accountability and personal liability for failures
Rising compliance costs draining internal resources
Reliance on critical third-party software vendors
We’ve built solutions specifically for these challenges, giving you the protection, documentation, and resilience you need — without drowning your teams in complexity.

Codekeeper's complete solutions for Cbw requirements
The Cybersecurity Act demands evidence of resilience, continuity, and supplier accountability. Codekeeper delivers all three with specialized escrow solutions that secure your critical software, simplify compliance, and prove you’re prepared when regulators call.
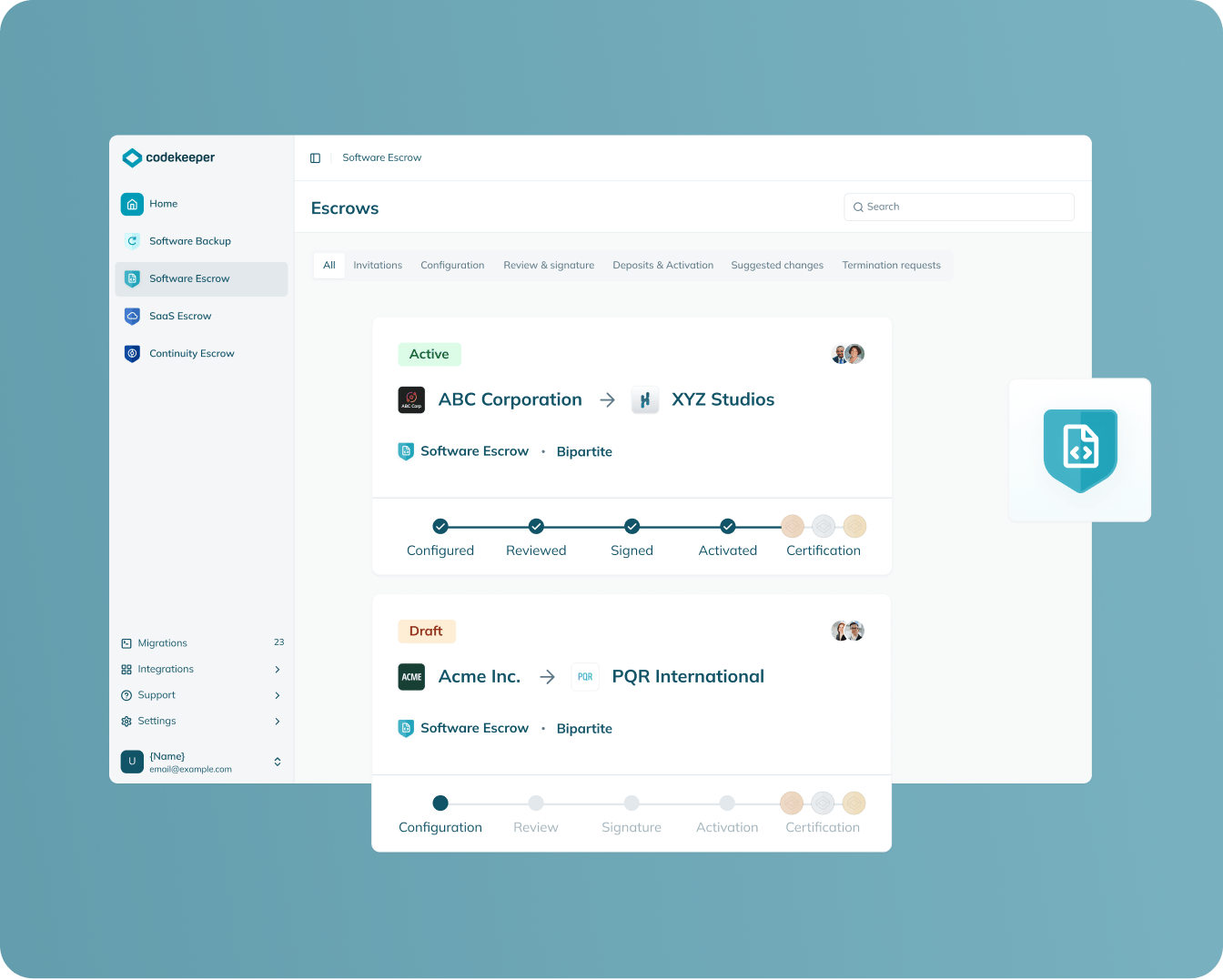
Software Escrow
Protection scope: On-premises software
Stores your on-premises applications securely so they remain recoverable if vendors fail.
Guarantees recovery access when suppliers disappear
Maintains essential functions during software disruptions
Reduces third-party dependency risks under the Cbw’s scope
Provides documented recovery proof for audits
Learn more
SAAS escrow
Protection scope: Cloud-based applications
Provides complete access to every component required to restore your SaaS platforms.
Ensures SaaS services continue during provider failures
Eliminates outages cascading across dependent systems
Sustains availability regardless of vendor disruption
Generates compliance documentation for regulators
Learn more

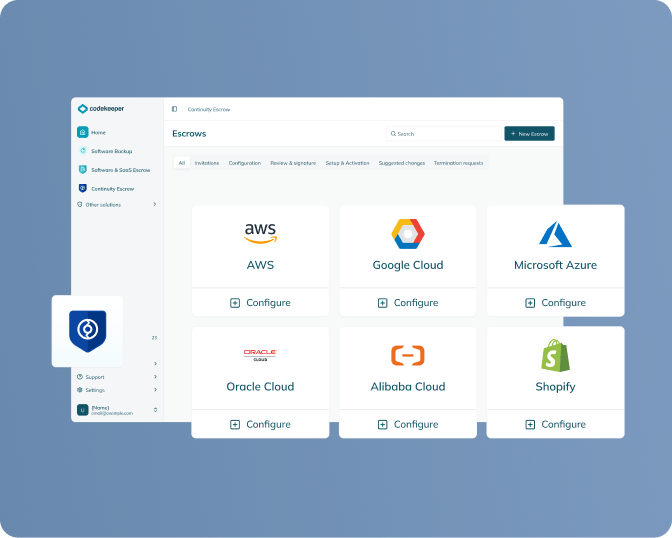
continuity escrow
Protection scope: Supporting infrastructure and services
Maintains critical vendor services by ensuring payments continue even during disruption.
Preserves essential supporting services during vendor failure
Prevents cascading interruptions across infrastructure
Delivers continuous operation during disputes or insolvency
Documents contingency planning for Cbw compliance
Learn more
Verification
Protection scope: All escrowed materials
Tests escrow deposits to check that they’re complete and usable when recovery is needed.
Validates assets actually work for restoration
Confirms realistic recovery timelines
Generates Software Resilience Certificates for Cbw audits
Strengthens trust with regulators and stakeholders
Learn more

Build Cybersecurity Act compliance in 4 easy steps
The Cbw requires organizations to prove resilience across their software supply chain. Codekeeper makes it simple with four clear steps.
1. Book your Cybersecurity Act demo
Let us review your applications and identify which are in scope under the Cbw.
2. Set up secure deposits
Your suppliers upload source code, configs, and technical materials into our encrypted vaults.
3. Verify your recovery assets
Our experts test escrowed materials to confirm they’re complete and ready for restoration.
4. Get your compliance proof
Receive Software Resilience Certificates and audit-ready reports that demonstrate Cbw compliance.
One call. One solution. End-to-end software resilience for the Cybersecurity Act.
Book a demo
Codekeeper takes the complexity out of compliance
Over the years, we’ve helped thousands of entities protect their critical software. Where the Cbw demands risk analysis, continuity plans, and supplier accountability, software escrow brings them together in a single, defensible control.
Cybersecurity Act enforcement timeline
-
October 17, 2024
EU deadline for all member states to transpose NIS2 into national law.Some Cbw provisions take partial direct effect in the Netherlands. -
June 2025
Cyberbeveiligingswet and accompanying decree submitted to the Dutch parliament.Draft text enters review phase in the Tweede Kamer and Council of State. -
Q3 2025 (expected)
Cbw scheduled to enter into force in the Netherlands. (If parliamentary approval lags, enforcement may shift into 2026.)Organizations begin formal compliance preparations under national law. -
2025 and onward
Food companies and other “important entities” face NVWA supervision under the Cbw.Broader Cbw obligations continue to expand as sector supervisors release detailed guidance.
October 17, 2024
EU deadline for all member states to transpose NIS2 into national law.
Some Cbw provisions take partial direct effect in the Netherlands.
June 2025
Cyberbeveiligingswet and accompanying decree submitted to the Dutch parliament.
Draft text enters review phase in the Tweede Kamer and Council of State.
Q3 2025 (expected)
Cbw scheduled to enter into force in the Netherlands. (If parliamentary approval lags, enforcement may shift into 2026.)
Organizations begin formal compliance preparations under national law.
2025 and onward
Food companies and other “important entities” face NVWA supervision under the Cbw.
Broader Cbw obligations continue to expand as sector supervisors release detailed guidance.
Note: The Cbw timeline will keep evolving as parliamentary approval, sectoral supervision, and EU peer reviews progress. Entities should act now, as deadlines and enforcement are only moving closer.
Why you can’t afford to miss Cbw deadlines
Failing to meet Cybersecurity Act requirements risks more than fines:
Severe financial penalties
The Cbw authorizes fines up to €10 million or 2% of global turnover for entities in scope, with penalties of €7 million or 1.4% for those classified as “important.”
Intrusive regulatory oversight
Authorities can conduct unannounced inspections, seize documentation, and issue binding remediation orders if they uncover gaps in your compliance.
Personal liability for management
Executives and board members carry direct responsibility. Regulators can impose fines and ban leaders from future roles.
Reputational and market damage
Regulators can expose non-compliance publicly, destroying customer trust and investor confidence while compliant competitors capture your market.
Forced service shutdowns
Supervisors can suspend critical services until you prove compliance, disrupting core functions your customers rely on.
Regulators won’t wait, and neither will cyber threats. Meeting the Cbw gives you control, stability, and trust.
How you benefit from compliance with the Cbw
Avoid heavy fines and shutdowns
Meeting Cbw requirements protects you from penalties of up to €10 million and prevents regulators from suspending your services.
Reduce risk for management
Clear compliance records show regulators your leadership acted responsibly, lowering the chance of personal liability.
Strengthen trust with partners
Customers, suppliers, and regulators know they can rely on you, opening doors that remain closed to less-prepared competitors.
Build resilience into your operations
Better continuity planning and verified recovery capabilities help you maintain critical services through supplier or system disruptions.

Protect your operations before Cbw penalties escalate
The Cyberbeveiligingswet is about to reshape cybersecurity obligations in the Netherlands. Don’t wait for regulators to intervene — act now to secure your compliance and prove your resilience.
Review of your Cbw compliance obligations
Overview of software escrow’s role in recovery and continuity
Practical guidance tailored to your sector and size
Ready-to-deploy solutions you can activate immediately
Frequently asked questions
What is the Cybersecurity Act (Cyberbeveiligingswet)?
The Cybersecurity Act (Cbw) is the Dutch law that implements the EU’s NIS2 directive. It sets strict rules for how “essential” and “important” entities manage risks, report incidents, and ensure continuity, replacing the older Wet beveiliging netwerk- en informatiesystemen (Wbni).
What is cybersecurity legislation?
Cybersecurity legislation sets the legal standards organizations must follow to protect systems and services against digital threats. In the EU, this takes shape through the NIS2 directive. In the Netherlands, those rules are applied through the Cbw.
Which sectors fall under the scope of the Cybersecurity Act?
The Cbw applies to large organizations in both essential and important sectors. Essential sectors include energy, healthcare, finance, transport, water, ICT services, digital infrastructure, public administration, and space. Important sectors include postal services, waste, chemicals, food, manufacturing, digital providers, and research.
When does the Cybersecurity Act take effect?
The Cbw is expected to take effect in the second half of 2025, though delays could push it into 2026. Some NIS2 provisions already apply directly in the Netherlands since October 17, 2024, but full obligations only begin once the Cbw is enacted.
Why is software escrow important for Cbw compliance?
Software escrow is important for Cbw compliance because it proves you can recover and keep systems running if a vendor fails. It secures your source code, SaaS components, and supporting services, so you can restore operations quickly and provide regulators with clear, audit-ready proof of compliance.
Can Codekeeper help with Cbw compliance?
Yes, Codekeeper provides escrow solutions that directly address Cbw requirements. We secure critical software assets, verify recovery capabilities, and supply compliance documentation so you can demonstrate resilience to supervisors without added complexity.


