ESMA
Eliminate software risk across your financial market infrastructures
Let Codekeeper’s state-of-the-art software escrows help you run stable operations that align with ESMA’s standards.

EU regulators now have clear guidance on when your external service and software relationships create regulatory red flags. Firms that can't demonstrate sufficient operational control face increased scrutiny and roadblocks to future growth.
ESMA: What you need to know
What is ESMA?
The European Securities and Markets Authority (ESMA) is the EU's financial markets regulator that oversees securities markets across all member states. Its new Principles on Third-Party Risks Supervision, issued in June 2025, provide national regulators with a framework to assess and supervise firms' outsourcing and vendor arrangements.
Who needs to comply with ESMA’s guidelines?
ESMA’s principles affect all EU securities market participants, including:
Asset and fund managers
Market operators
Asset and fund managers
Asset and fund managers
Asset and fund managers
Key ESMA principles
ESMA's third-party risk supervision principles require EU securities market participants to implement these four key controls to prevent "empty shell" operations:
1
Maintain effective governance and corporate substance with boards retaining oversight and adequate EU presence.
2
Establish comprehensive risk management frameworks with thorough assessments before entering arrangements.
3
Formalize vendor relationships through contracts with audit rights, due diligence, and ongoing monitoring.
4
Address specific risks from non-EU providers, supply chains, and outsourcing of control functions.
The software escrow — ESMA connection
Software escrow directly addresses ESMA's third-party risk supervision requirements by ensuring operational resilience and preventing excessive technological dependency.
ESMA risk
Critical software providers fail suddenly
Supervisors identify firms with inadequate exit strategies
Uncontrolled vendor dependencies
Software escrow solution
Secures source code and technical dependencies
Triggers legal release when vendors fail
Enables independent system operation
Compliance outcome
Maintained operating licenses and market access
Avoided emergency system rebuilds costing millions
Accelerated regulatory approval processes
When ESMA supervisors discover you can't execute your documented exit strategies, your authorization is in immediate jeopardy. Without escrow, you're betting your firm's survival on vendor relationships you can't control and technical assets you don't own.
Let us help you align with ESMA's third-party risk guidelines
Codekeeper brings together expertise in EU financial regulations and software protection, with tailored solutions for securities market participants managing supplier risk supervision.
We understand the regulatory challenges you're facing:
Interpreting evolving ESMA oversight standards across jurisdictions
Balancing operational efficiency with regulatory independence requirements
Documenting comprehensive exit strategies that satisfy supervisory review
Managing software vendor relationships while keeping control over your systems
We're safeguarding mission-critical software for financial institutions across Europe. We can strengthen your operational independence, too.

Codekeeper's complete solutions for ESMA software risk supervision
Our escrow solutions help EU financial institutions maintain operational independence and demonstrate effective third-party oversight while protecting critical software investments.
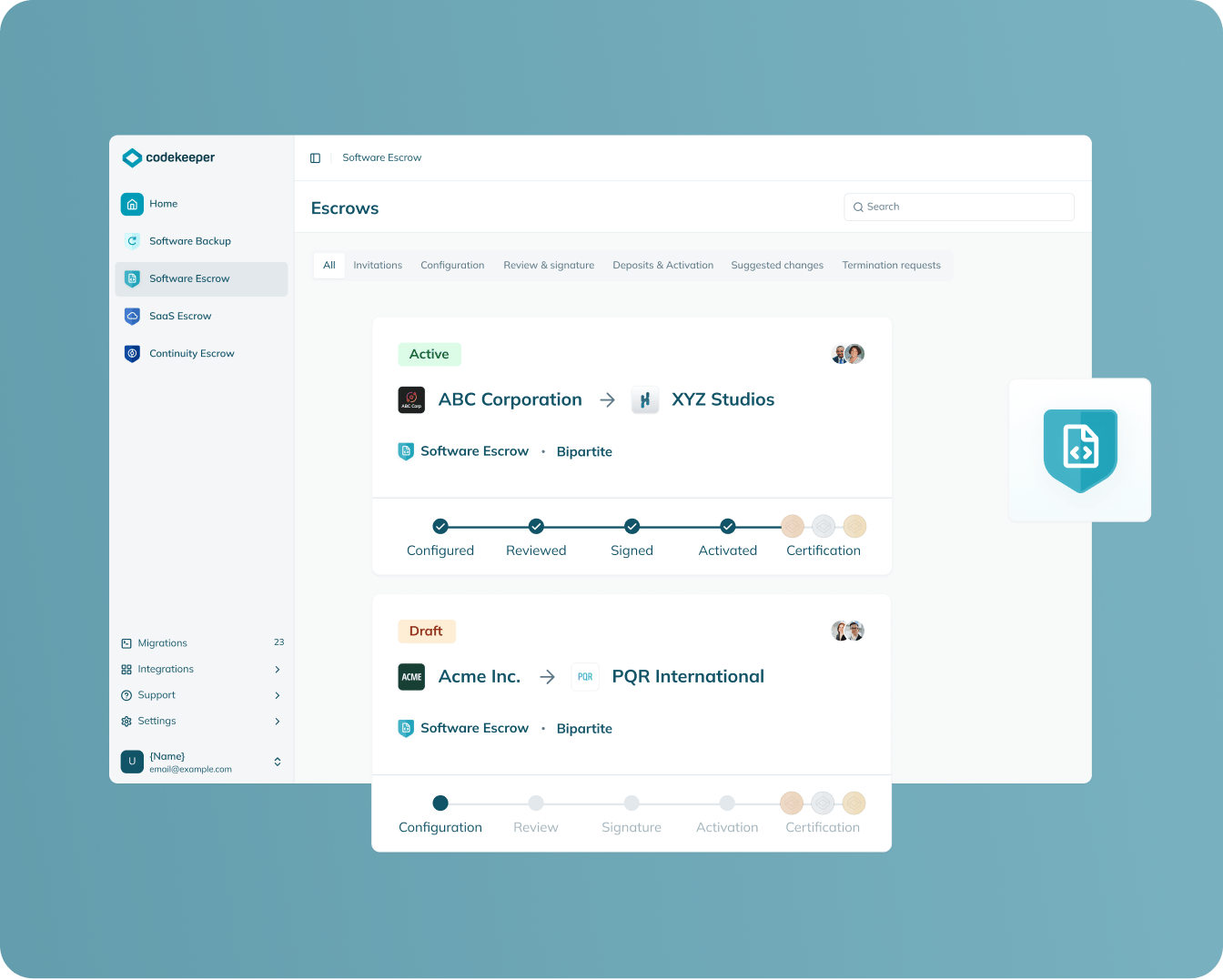
Software Escrow
Protection scope: On-premises financial software
Stores complete source code, data, and documentation for on-premises financial applications in secure vaults.
Enables independent system reconstruction when vendors terminate relationships
Provides tangible proof of exit strategy implementation to supervisors
Maintains technical self-sufficiency required for regulatory approval
Eliminates vendor lock-in that could compromise operational substance
Learn more
SAAS escrow
Protection scope: Cloud-based financial applications
Captures source code, APIs, database schemas, configuration files, and deployment scripts needed to recreate critical SaaS applications.
Gives you independence from cloud service providers
Delivers concrete recovery plans for modern technology architectures
Satisfies due diligence requirements for third-party cloud arrangements
Creates audit trails that supervisors expect during regulatory examination
Learn more

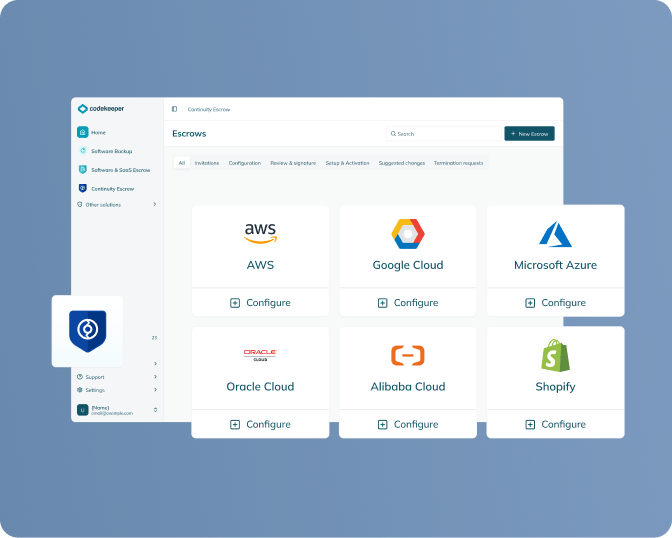
Continuity escrow
Protection scope: Supporting services and infrastructure
Maintains payments to essential service providers during vendor transitions or failures.
Prevents service disruptions from triggering emergency regulatory notifications
Manages complex supply chain dependencies across multiple vendor layers
Buys essential transition time without operational interruption
Supports board accountability for third-party oversight responsibilities
Learn more
Verification
Protection scope: All escrowed materials
Independently tests source code, configurations, and documentation to prove they're complete and can rebuild working systems.
Converts theoretical exit plans into verified operational capabilities
Establishes realistic recovery timelines based on actual testing results
Generates regulatory-grade evidence of business continuity preparedness
Produces certificates demonstrating compliance readiness for supervisory review
Learn more

Align with ESMA's third-party risk expectations in 4 simple steps
ESMA's principles require EU securities firms to demonstrate operational independence and effective vendor oversight. Here's how to strengthen your supervisory position:
1. Book your ESMA readiness assessment
We'll evaluate your software dependencies and identify which arrangements need stronger exit strategies for regulatory review.
2. Select your software protection approach
Choose from Software Escrow, SaaS Escrow, or Continuity Escrow based on your technology architecture and critical vendor relationships.
3. We handle vendor coordination and legal setup
Our team manages all vendor onboarding, drafts escrow agreements, and establishes automated deposit processes without disrupting your operations.
4. Receive your compliance documentation
Get verification reports and Software Resilience Certificates that demonstrate concrete exit capabilities and effective third-party risk management to supervisors.
One call. One solution. Complete software risk framework alignment for ESMA expectations.
Book a free demo
Codekeeper takes the complexity out of software risk management
Over the years, we've helped thousands of financial institutions protect their critical software dependencies without getting overwhelmed by regulatory expectations. Our solutions make ESMA's third-party risk supervision principles straightforward and manageable.
ESMA third-party risk supervision timeline
-
June 12, 2025
ESMA principles published — Guidance issued to promote supervisory convergence across EU member states -
2025 onwards
Enhanced supervisory scrutiny during authorization reviews, ongoing supervision, and material change assessments
June 12, 2025
ESMA principles published — Guidance issued to promote supervisory convergence across EU member states
2025 onwards
Enhanced supervisory scrutiny during authorization reviews, ongoing supervision, and material change assessments
The dangers of insufficient third-party oversight
When you can't show you have proper control over your vendor relationships, you face growing regulatory problems that can seriously damage your business.
Authorization delays and denials
Regulators can block your applications for new licenses when you can't prove you have enough in-house capabilities or realistic plans for switching vendors if things go wrong.
Ongoing supervisory restrictions
Your regulator may limit what you can do, demand extra reports, or restrict your business activities when they think your vendor management is too weak during routine reviews.
Blocked business expansion
Major changes to your outsourcing deals can trigger regulatory reviews that prevent you from launching new products, entering new markets, or buying other companies.
Increased compliance costs
Firms with poor vendor oversight get put under the microscope more often, requiring expensive extra documentation, frequent reports, and potentially costly changes to how you operate.
Competitive disadvantage
While your competitors with strong vendor management operate freely, you'll face regulatory roadblocks that slow down growth and limit your strategic options.
These risks don't have to be your reality. Take control of your vendor relationships now.
E-BOOK
The CRA: Your Complete Compliance Guide
Fill in the form below to get expert guidance on meeting Europe's cybersecurity requirements for connected products.

*E-book available only in English
Get your free CRA compliance guide
How you can benefit from strong software risk management
Smoother regulatory interactions
Show regulators you have proper vendor controls in place, which leads to faster license approvals, fewer questions from supervisors, and easier regulatory reviews.
Better operational resilience
Create real independence from critical vendors with concrete backup plans, which reduces business disruption risks and keeps services running when vendor relationships change.
Competitive market advantage
Operate with more strategic flexibility while competitors face regulatory roadblocks, so you can expand into new markets and services faster without supervisory delays.
Lower compliance costs
Avoid expensive emergency vendor replacements, costly operational changes, and intensive regulatory scrutiny that wastes resources and management time.
Stronger board confidence
Give directors documented proof of effective risk management, which supports better decision-making and shows proper oversight to stakeholders.

Don't let vendor dependencies put your authorization at risk
Our team will evaluate your third-party arrangements and show you how software escrow creates the operational independence ESMA supervisors expect from EU securities firms.
Analysis of your critical vendor relationships and exit strategy gaps
Demonstration of how software escrow addresses ESMA's "sufficient substance" requirements
Step-by-step guidance for implementing effective vendor risk controls
Documentation that proves operational resilience to your supervisors
Frequently asked questions
What is the ESMA regulation?
ESMA's Principles on Third-Party Risks Supervision are non-binding guidance issued in June 2025 by the European Securities and Markets Authority. These principles help EU regulators supervise how securities firms manage their outsourcing and vendor relationships, with the goal of preventing firms from becoming "empty shells" that lack sufficient operational control.
Is ESMA mandatory?
ESMA’s principles themselves are non-binding guidance, not legal requirements. However, regulators use them to interpret existing mandatory EU securities laws like MiFID II, EMIR, and UCITS. Firms that align with ESMA's expectations typically face smoother regulatory interactions and fewer supervisory challenges.
What is an "empty shell" entity?
An "empty shell" (also called "letter box entity") is a firm that has outsourced so many critical functions that it lacks sufficient staff, technical capabilities, or operational control to function independently. ESMA is concerned about these entities because they're difficult to supervise effectively and may not be able to comply with regulations without their third-party providers.
How are ESMA and DORA linked?
ESMA and DORA both address third-party risks but focus on different aspects. DORA specifically covers ICT (information and communication technology) services like cloud hosting, cybersecurity tools, and data centers. ESMA's principles cover all other third-party arrangements in securities markets, including business software, operational services, and vendor relationships. Some software systems may need to comply with both frameworks — the ICT infrastructure requirements under DORA and the business relationship and exit strategy requirements under ESMA's principles.
Why is software escrow relevant to ESMA?
ESMA requires firms to have concrete exit strategies for vendor relationships and maintain operational independence. Software escrow provides this by storing source code and technical documentation so you can continue operations if software vendors fail or terminate contracts. This demonstrates the operational resilience ESMA supervisors expect.
Can Codekeeper help with ESMA readiness?
Yes, Codekeeper’s software escrow solutions create the documented exit strategies ESMA requires. We secure your critical software assets — source code, technical specifications, and recovery materials — and provide concrete evidence to supervisors that you maintain operational independence from vendors.


