ISO 27001
Build ISO 27001-ready supply chain resilience with software escrow
Protect your critical information assets and establish robust ICT supply chain security with Codekeeper's specialized software escrow solutions.

When your critical software vendors fail, your ISO 27001 controls crumble. Your organization faces immediate compliance gaps, system vulnerabilities, and lost certifications that destroy business credibility.
ISO 27001: What you need to know
What is ISO 27001?
ISO 27001 is the international standard for information security management systems (ISMS). It provides a structured framework for organizations to protect their sensitive data through risk-based security controls, ensuring the confidentiality, integrity, and availability of information assets.
Who needs to comply with ISO 27001?
ISO 27001 applies to any organization that wants to demonstrate unified information security management. While certification is voluntary, it's increasingly required by:
Technology companies
Software developers, cloud providers, and IT service companies
Financial services
Banks, insurance companies, and fintech organizations
Healthcare organizations
Hospitals, medical device manufacturers, and health tech companies
Government contractors
Organizations handling sensitive public sector data
Manufacturing
Companies with connected systems and digital supply chains
Professional services
Legal firms, consultancies, and outsourcing providers
Many organizations pursue ISO 27001 to meet contractual requirements from clients, comply with regulations like GDPR, or demonstrate security capabilities in competitive tenders.
Key ISO 27001 requirements
ISO 27001:2022 requires organizations to implement a comprehensive information security management system (ISMS) through these foundational controls:
1
Define and document your ISMS framework.
2
Conduct regular risk assessments and apply appropriate safeguards.
3
Secure supplier relationships and manage third-party risks.
4
Maintain business continuity and disaster recovery plans.
5
Monitor and audit security controls for continuous improvement.
6
Test backups and recovery procedures for critical systems.
The software escrow — ISO 27001 connection
Software escrow directly supports ISO 27001 compliance by addressing critical supplier relationship and business continuity requirements outlined in Annex A controls.
ISO 27001 risk
Critical suppliers go out of business or drop support
Loss of source code blocks updates and recovery
Vendor failures disrupt continuity and resilience
Audits expose weak supplier oversight
Software escrow solution
Escrow vaults store code, docs, and recovery assets
Legal framework guarantees access if suppliers fail
Verified deposits ensure completeness for recovery
Automated deposits create a compliance audit trail
Compliance outcome
Vendor dependencies secured as recoverable assets
Supplier controls verified within certified ISMS
Continuity assured despite third-party disruptions
Risk management evidenced with audit-ready records
When ISO 27001 auditors ask how you'll maintain operations if software vendors fail, escrow provides documented proof. Without it, you can't demonstrate the supplier risk controls that certification requires.
Let us help you with ISO 27001 readiness
Codekeeper brings together expertise in information security management and software protection with tailored solutions for organizations pursuing ISO 27001 certification.
We see the challenges you face:
Complex supplier relationship requirements with extensive documentation needs
Mounting pressure to manage third-party risks
Uncertainty about which controls to implement for effective ISMS compliance
Continuous dependency on critical software vendors without backup plans
We've secured critical software assets for thousands of organizations globally, helping them build the supplier resilience foundation that ISO 27001 demands. We can strengthen your information security management, too.

Codekeeper's complete solutions for ISO 27001 requirements
Our escrow solutions help meet ISO 27001's supplier relationship and business continuity standards while securing your most critical software dependencies.
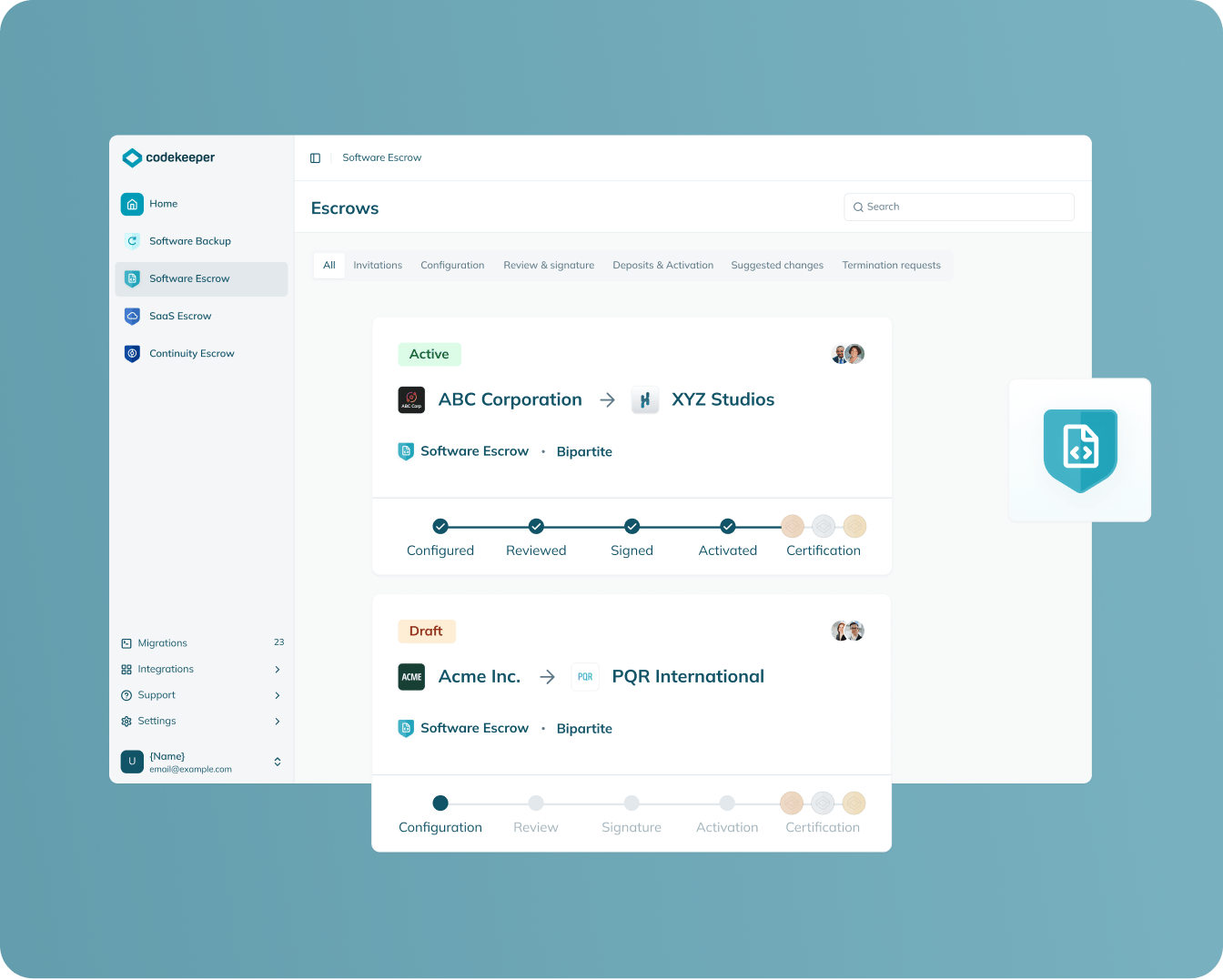
Software Escrow
Protection scope: On-premises software and applications
Safeguards traditional on-premises systems with a legal framework that ensures continuous access to critical software assets when vendors fail.
Documents your control over third-party software risks
Establishes verifiable recovery capabilities for critical business operations
Creates clear audit trail for supplier risk management processes
Provides compliance-ready evidence of proactive third-party risk mitigation
Learn more
SAAS escrow
Protection scope: Cloud-based applications and services
Protects cloud-based applications with comprehensive deposits that include everything needed to maintain operations if SaaS providers fail.
Extends third-party risk management to modern cloud service dependencies
Guarantees recovery of essential online services when disruptions occur
Addresses the growing migration to SaaS applications in your risk assessments
Delivers documented compliance evidence for cloud-first technology environments
Learn more

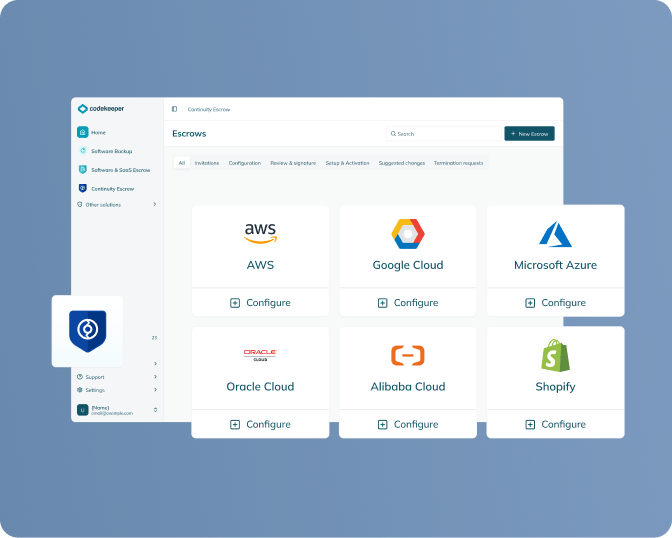
Continuity escrow
Protection scope: Supporting infrastructure and services
Takes over payments for supporting services and infrastructure to maintain critical operations when vendor relationships break down.
Manages cascading risks from your vendor's dependencies
Reduces the likelihood of business disruption that compromises information security
Creates operational continuity documentation that satisfies audit requirements
Supports coordinated oversight of complex vendor ecosystems
Learn more
Verification
Protection scope: All escrowed materials
Tests escrowed assets to confirm they're complete and usable, with clear documentation that meets regulatory expectations for systematic risk management.
Validates recovery capabilities with independently verified evidence
Establishes realistic recovery timeframes for business continuity planning
Generates testing documentation required for comprehensive risk assessments
Provides Software Resilience Certificates for formal compliance records
Learn more

Get ISO 27001 ready in 4 simple steps
ISO 27001 requires you to demonstrate control over your critical software dependencies and vendor relationships. Here's how to build that foundation quickly:
1. Schedule your ISO 27001 assessment call
We'll evaluate your software portfolio and identify which applications require escrow protection to meet ISO 27001 supplier relationship requirements.
2. Select your escrow strategy
Choose standard software escrow protection or add verification testing for comprehensive evidence of recovery capabilities and risk management controls.
3. Complete implementation with our support
Our specialists coordinate all vendor arrangements, draft legal frameworks, and establish automated processes without burdening your internal teams.
4. Receive your compliance documentation
Get verified proof of your supplier risk management capabilities, including Software Resilience Certificates for audit evidence.
One consultation. One solution. Complete third-party risk management for ISO 27001 certification readiness.
Book a free demo
Codekeeper takes the complexity out of compliance
Over the years, we've helped thousands of organizations protect their critical software without drowning in technical details. Our solutions make ISO 27001 requirements straightforward and manageable.
ISO 27001:2022 transition timeline
The ISO 27001 standard has evolved significantly with the 2022 update. Whether you're pursuing initial certification or updating an existing certificate, understanding these key dates helps you plan your implementation strategy and avoid certification delays.
-
October 2022
ISO 27001:2022 officially published with updated Annex A controlsOrganizations begin transition planning from 2013 version -
April - May, 2024
Final deadline for new certifications under ISO 27001:2013All certification bodies must use 2022 version for new audits -
October 31, 2025
Transition deadline for existing ISO 27001:2013 certificatesOrganizations must complete recertification to 2022 version or lose certification -
Ongoing from 2025
Continuous surveillance audits under new control frameworkRegular management reviews and risk assessments required for maintained certification
October 2022
ISO 27001:2022 officially published with updated Annex A controls
Organizations begin transition planning from 2013 version
April - May, 2024
Final deadline for new certifications under ISO 27001:2013
All certification bodies must use 2022 version for new audits
October 31, 2025
Transition deadline for existing ISO 27001:2013 certificates
Organizations must complete recertification to 2022 version or lose certification
Ongoing from 2025
Continuous surveillance audits under new control framework
Regular management reviews and risk assessments required for maintained certification
The cost of inadequate information security management
Without supplier risk management and continuity planning, organizations risk cascading failures that erase years of investment and trust.
Lost business opportunities
Without ISO 27001 certification, you risk exclusion from high-value contracts in finance, healthcare, and government.
Devastating data breaches
Supplier failures expose critical systems, with breaches costing an average of $4.44M globally.
Regulatory scrutiny and penalties
Regulators like GDPR authorities impose severe fines on organizations that can't demonstrate structured information security management.
Mission-critical operations forced offline
When key vendors fail without escrow, essential systems go dark. Recovery can take weeks or months while teams rebuild or replace applications.
Reputation destruction
When security or compliance failures surface, brand credibility suffers. The fallout can include lost trust, broken partnerships, and years of reputational damage.
Don't let vendor failures derail your ISO 27001 certification. Secure your supplier risk management now.
E-BOOK
The CRA: Your Complete Compliance Guide
Fill in the form below to get expert guidance on meeting Europe's cybersecurity requirements for connected products.

*E-book available only in English
Get your free CRA compliance guide
How you benefit from ISO 27001 readiness
Win more business with trusted credentials
ISO 27001 certification opens doors to contracts in finance, healthcare, and government. It also reduces security questionnaires, speeding up procurement and sales cycles.
Strengthen risk management and prevent incidents
ISO 27001's structured approach to risk assessment and control implementation helps identify vulnerabilities before they become costly problems.
Build stakeholder confidence and market credibility
ISO 27001 certification proves to customers, investors, and partners that security is a priority. It signals organizational maturity and creates competitive differentiation.
Create systematic operational resilience
ISO 27001's continuous improvement framework ensures your security posture improves over time rather than becoming outdated.

Shield your supplier relationships before gaps become crises
Our compliance specialists will show you exactly how our escrow solutions address ISO 27001's supplier relationship and business continuity requirements while safeguarding your critical software dependencies.
Personalized assessment of your third-party risk management needs
Clear explanation of how escrow satisfies ISO 27001 control requirements
Straightforward guidance without overwhelming technical complexity
Actionable implementation steps you can begin immediately
Frequently asked questions
What is ISO 27001 in a nutshell?
ISO 27001 is the international standard for information security management. It provides a structured framework to protect your data through systematic risk assessments and security controls. While certification is voluntary, it's globally recognized as proof that your organization handles information security according to established best practices.
What are the three principles of ISO 27001?
ISO 27001 is built around the CIA triad: Confidentiality ensures only authorized people can access information, Integrity maintains data accuracy and completeness, and Availability guarantees information is accessible when needed. These three principles guide every security control and risk management decision within your ISMS.
Is ISO 27001 hard to get?
ISO 27001 certification is achievable with the right approach and commitment. The key is understanding why you need an ISMS and how your organization can align with the standard's requirements. Most organizations complete certification in six to 18 months, but building an effective ISMS requires ongoing commitment to continuous improvement and integrating security considerations into every business decision.
What is the difference between ISO 27001 and SOC 2?
ISO 27001 and SOC 2 serve different purposes in information security. ISO 27001 helps any organization establish a comprehensive information security management system, requiring you to build an entire risk-based framework with policies, procedures, and continuous improvement processes. SOC 2, on the other hand, is designed for service companies and evaluates their existing controls against predetermined criteria for security, availability, processing integrity, confidentiality, and privacy.
Why is software escrow important for ISO 27001 certification?
Software escrow aligns with ISO 27001 requirements for supplier relationship management and business continuity planning. When critical software vendors fail, escrow ensures continued access to source code and recovery materials. This provides auditable evidence of third-party risk mitigation that certification bodies expect to see during ISO 27001 assessments.
Can Codekeeper help with ISO 27001 readiness?
Yes, Codekeeper provides specialized software escrow solutions that address specific ISO 27001 control requirements around supplier relationships and operational resilience. Our platform secures critical software assets, establishes legal frameworks for vendor risk management, and generates compliance documentation, including Software Resilience Certificates.


