NIS2
Achieve NIS2 compliance with bulletproof software resilience
Ensure software supply chain security and meet NIS2 compliance requirements with Codekeeper’s specialized escrow solutions that safeguard your essential digital services across the EU.
When cyber attackers breach your critical infrastructure, the damage can spread instantly. Your essential services face potential shutdown, public safety risks, and severe regulatory consequences that could devastate your operations.
The NIS2 directive: What you need to know
What is NIS2?
The Network and Information Systems Directive 2 (NIS2) is a stringent regulation that requires vital sectors to improve their cybersecurity measures, incident response plans, and reporting mechanisms. Its mission? To create a high common level of cybersecurity across the EU, keep essential services running, and protect the economy (and society) from cyber incidents.
Who needs to comply with the NIS2 directive?
NIS2 divides entities into two groups: “essential” and “important.” Compliance obligations apply to both, though essential entities must follow stricter rules. NIS2 is relevant to the following sectors:
Energy
Essential entity
Transport
Essential entity
Finance
Essential entity
Healthcare
Essential entity
Digital infrastructure
Essential entity
Water supply
Essential entity
ICT-service management
Essential entity
Public administration
Essential entity
Space
Essential entity
Postal services
Important entity
Waste management
Important entity
Chemicals
Important entity
Food
Important entity
Manufacturing
Important entity
Digital providers
Important entity
Research
Important entity
Key NIS2 requirements
The NIS2 directive requires essential and important entities to implement six key controls to boost cyber resilience:
1
Implement comprehensive risk management practices and policies to handle cybersecurity risks.
2
Manage cybersecurity risks from suppliers and ensure they follow security standards.
3
Establish and maintain appropriate mechanisms to recover from cybersecurity incidents.
4
Develop continuity and recovery plans and test them to ensure service resilience during a cyber incident.
5
Report significant cyber incidents to relevant national authorities.
6
Take extra steps to secure critical digital services that society and the economy need.
Note: All sectors in scope must report cyber incidents, but regulators monitor essential entities continuously, while important entities only get inspected after something goes wrong. Both can face heavy penalties if they don't comply.
The software escrow — NIS2 connection
Software escrow creates a direct pathway to NIS2 compliance by boosting supply chain security and enhancing vendor resilience and accountability.
NIS2 risk
Critical software suppliers suddenly fail or get compromised
Your essential services face immediate shutdown
You can't recover from vendor-related cyber incidents
Management faces personal liability for supply chain failures
Software escrow solution
Stores critical software assets for immediate system recovery
Ensures you can rebuild services when suppliers fail
Demonstrates your recovery plans actually work
Documents your due diligence in supplier risk management
Compliance outcome
Satisfied NIS2 supply chain security requirements
Reduced exposure to cascading supply chain cyber incidents
Proven business continuity and disaster recovery capabilities
Protection from €10 million fines and management penalties
Let us help you achieve NIS2 compliance
Codekeeper brings together expertise in EU cybersecurity regulations and software protection, with tailored solutions for essential and important entities.
We understand the obstacles ahead:
Comprehensive cybersecurity measures across core EU sectors
Management accountability with personal liability exposure
Complex supply chain security assessments and documentation
Continuous dependency on critical software suppliers
We’re protecting vital software systems for thousands of organizations globally. We can lock down your cyber resilience, too.

Codekeeper's complete solutions for NIS2 requirements
Our state-of-the-art escrow solutions help you meet NIS2's cybersecurity risk management and incident response requirements while securing your essential software infrastructure.
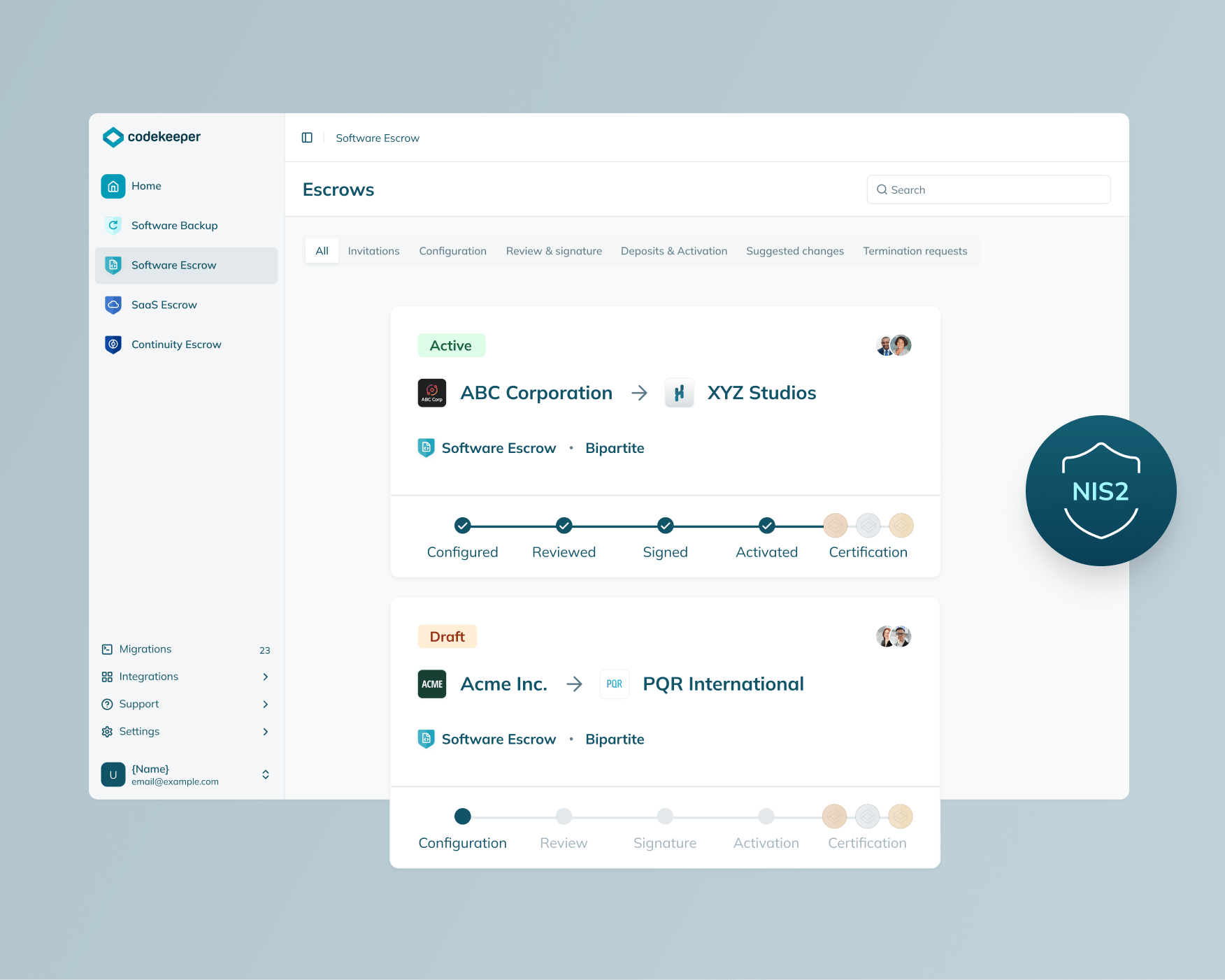
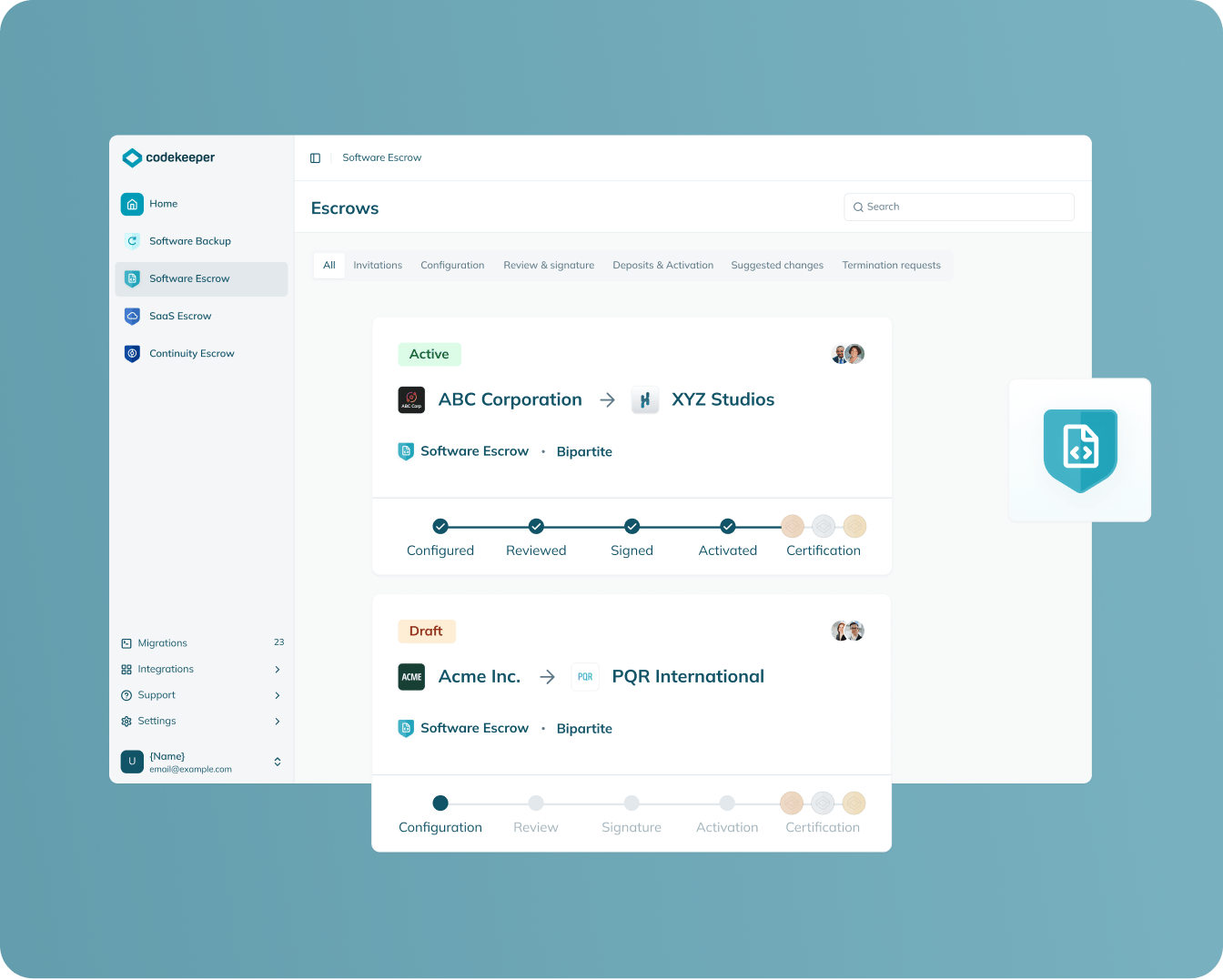
Software Escrow
Protection scope: Traditionally installed software
Secures your on-premises software assets in encrypted vaults with immutable storage for NIS2-compliant supplier risk management.
Fulfills mandatory supply chain due diligence requirements
Creates audit-ready evidence of vendor oversight for competent authorities
Establishes legal recovery rights when critical suppliers fail
Demonstrates concrete risk mitigation to satisfy regulatory expectations
Learn more
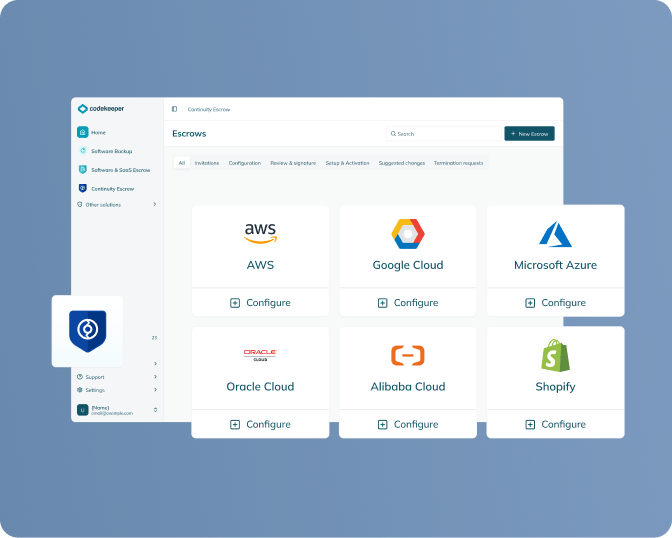
SAAS escrow
Protection scope: Cloud-based applications
Captures all components needed for SaaS cloud recovery — source code, configurations, deployment scripts, and dependencies.
Secures digital infrastructure against third-party provider failures
Provides verified recovery capabilities for incident response plans
Addresses system dependencies under NIS2 scope
Generates documentation proving supplier security assessments
Learn more

continuity escrow
Protection scope: Supporting infrastructure and services
Maintains payment flows to critical service providers, preventing vendor-related disruptions that could trigger NIS2 incident reporting.
Guards against service interruptions when vendors face financial difficulties
Eliminates cascading supply chain failures from vendor bankruptcies
Buys time to find replacement vendors without service interruption
Documents contingency planning for third-party service dependencies
Learn more
Verification
Protection scope: Software and SaaS applications
Rigorously tests escrowed materials to confirm operational viability with detailed reporting designed for strict regulatory oversight.
Proves recovery capabilities through independent testing protocols
Documents realistic restoration timelines for emergency response planning
Supports NIS2's mandatory effectiveness assessment requirements
Generates Software Resilience Certificates proving compliance readiness
Learn more

Build NIS2 compliance in 4 simple steps
NIS2 requires you to secure your software supply chain against cyber threats. Here's how to strengthen your critical infrastructure:
1. Book a free demo
We'll evaluate which essential service applications create cybersecurity risks under NIS2's expanded coverage requirements.
2. Set up secure asset deposits
Your critical suppliers upload their source code, security patches, and technical specs into our escrow vaults.
3. Our escrow experts review your escrowed materials
We check your assets for vulnerabilities and confirm they can restore services during cyber incidents.
4. Get your Software Resilience Certificate
Receive verified proof that you can rebuild essential software infrastructures even when your suppliers fail.
One call. One solution. Complete software resilience compliance for NIS2.
Book a free demo
Codekeeper takes the complexity out of compliance
Over the years, we've helped thousands of critical entities protect their software without drowning in technical details. Our solutions make regulatory requirements straightforward and manageable.
NIS2 enforcement timeline
-
October 17, 2024
Member state transposition deadline — NIS2 should be incorporated into national laws -
January 17, 2025
Peer review methodologies established by the NIS Cooperation Group (made up of representatives of Member States, the European Commission, and ENISA) -
April 17, 2025
Entity registration lists due from member states to the European Commission -
October 17, 2027
First effectiveness review potentially introducing new cybersecurity requirements
October 17, 2024
Member state transposition deadline — NIS2 should be incorporated into national laws
January 17, 2025
Peer review methodologies established by the NIS Cooperation Group (made up of representatives of Member States, the European Commission, and ENISA)
April 17, 2025
Entity registration lists due from member states to the European Commission
October 17, 2027
First effectiveness review potentially introducing new cybersecurity requirements
The cost of ignoring NIS2 requirements
Failing to meet NIS2 standards unleashes devastating consequences across your critical operations:
Severe monetary sanctions
Your organization faces up to €10 million or 2% of global turnover for essential entities — €7 million or 1.4% for important entities.
Leadership prosecution
Your CEO and board members risk criminal liability, personal financial penalties, and career-ending bans from executive roles.
Business comes to a standstill
National cybersecurity authorities force the immediate closure of your critical services until you prove adequate security measures.
Authorities take control
Government inspectors conduct unannounced inspections, seize documentation, and impose binding remediation orders on your operations.
European regulators have zero tolerance for weak cybersecurity in critical sectors. Build your resilience now so they can’t build a case against you.
E-BOOK
Assess, plan, implement: Your guide to NIS2 compliance
Fill in the form below to learn more about meeting NIS2's cybersecurity risk management requirements.
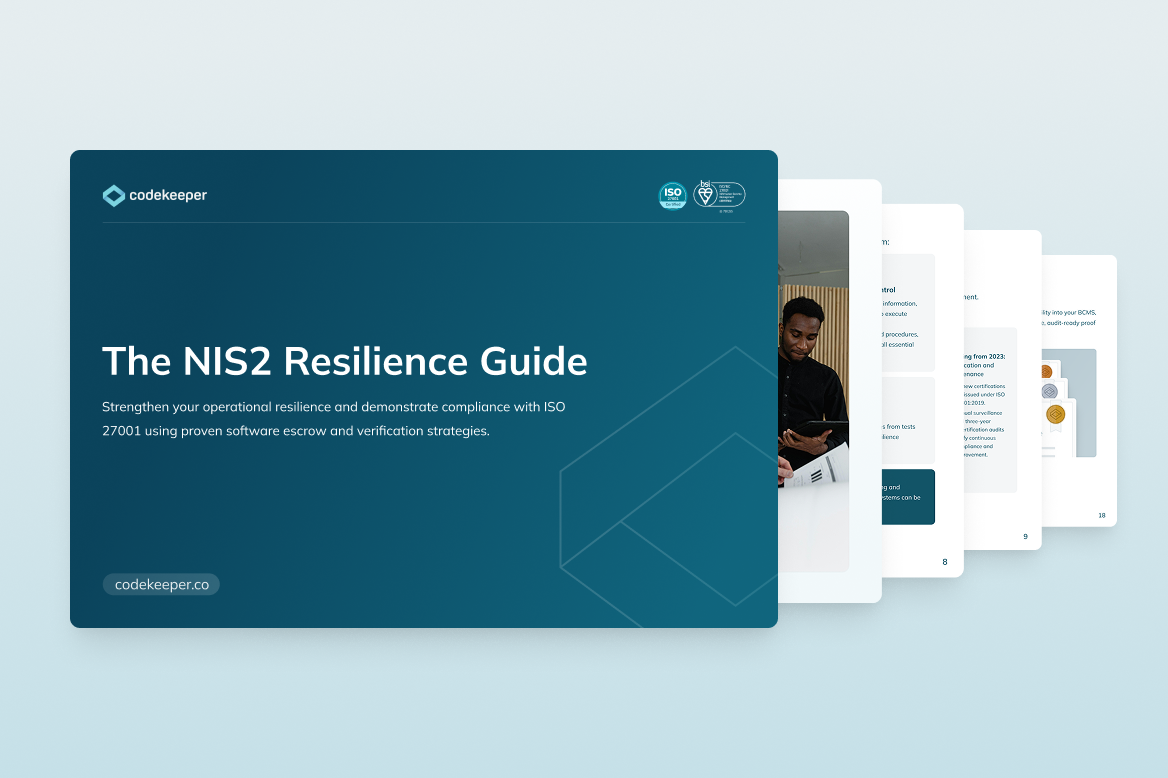
*E-book available only in English
Get your free NIS2 guide now
How you benefit from NIS2 compliance
Secure your critical operations
NIS2 compliance helps you avoid €10 million fines and prevents authorities from shutting down your operations. While non-compliant competitors get locked out of EU markets, you can keep operating across all 27 member states.
Protect executive leadership
Show regulators that your management team takes cybersecurity seriously to avoid criminal charges and career-ending penalties. Compliance proves your leaders did their job of managing supplier risks and incident response.
Strengthen vendor partnerships
Companies that need NIS2-compliant partners will choose you over competitors who can't prove their cybersecurity standards. Your compliance documentation opens doors to contracts that non-compliant teams can't access.
Build operational resilience
Turn required cybersecurity measures into business advantages by building better incident response and continuity plans. When cyber attacks hit, you'll recover faster than competitors, all while keeping essential services running.

Protect your critical services before penalties escalate
Our compliance advisors will show you exactly how our software escrow solutions help you meet NIS2’s cyber resilience standards and secure your essential service operations.
Review of your vendor risk management obligations
Overview of software escrow's role in incident response planning
Straightforward explanation of NIS2’s expectations
Ready-to-deploy escrow solutions you can activate today
Frequently asked questions
Is NIS2 mandatory?
Yes, NIS2 is mandatory for all “essential” or “important” EU entities in sectors like energy, transport, banking, and healthcare.
How does NIS2 build on the original NIS directive?
NIS2 broadens the scope of the original directive, expands the range of entities covered, strengthens security requirements, enhances supply chain security, and pushes for stricter incident reporting laws.
How will NIS2's regulations be monitored and enforced?
Member States are responsible for implementing and enforcing NIS2. This may involve establishing national competent authorities to oversee compliance and impose sanctions for non-compliance.
When does NIS2 take effect in the Netherlands?
NIS2 will be implemented in the Netherlands as the Cybersecurity Act (Cyberbeveiligingswet) and will take effect in early 2026. Many organizations will be directly or indirectly affected by this legislation, either through their own compliance obligations or requirements from clients and partners.
How does NIS2 relate to other EU cybersecurity policies?
NIS2 focuses on operational cybersecurity for critical service providers, while the Cyber Resilience Act (CRA) ensures the digital products they use are secure by design. Together with regulations, like GDPR and DORA, they create a comprehensive EU cybersecurity framework that covers services, products, data protection, and financial resilience.
Which basic measures does the NCSC recommend?
The National Cyber Security Centre (NCSC) recommends basic measures such as effective access control, secure configuration, network security, malware protection, and patch management.
What's the difference between essential and important entities under NIS2?
Essential entities (typically 250+ employees, €50M+ turnover) in highly critical sectors face proactive supervision and higher penalties (€10M or 2% of global revenue). Important entities (50-250 employees, €10M+ turnover) are subject to reactive supervision and lower penalties (€7M or 1.4% of global revenue).


