SOC 2
Build SOC 2-ready vendor risk management with software escrow
Meet AICPA's trust criteria with Codekeeper’s state-of-the-art escrow solutions for service organizations.

When SOC 2 auditors find gaps in your software continuity planning, your compliance timeline crashes. Your organization faces extended audit cycles, escalating compliance costs, and prospects who won't wait for your certification.
SOC 2: What you need to know
What is SOC 2?
SOC 2 is a compliance framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates how well service organizations protect customer data and maintain operational integrity.
Who needs to comply with SOC 2?
SOC 2 affects service organizations that store, process, or transmit customer data, particularly those targeting enterprise clients. While compliance is voluntary, it's become a business necessity for:
Technology companies
SaaS providers, cloud service providers, data centers, hosting companies, and software development firms
Service organizations
Payment processors, healthcare technology providers, financial services platforms, and HR and payroll systems
Digital infrastructure
Cybersecurity vendors, telecommunications providers, managed service providers, and IT consulting firms
Key SOC 2 requirements
SOC 2 compliance requires service organizations to implement comprehensive controls across five trust service criteria that protect customer data and ensure operational resilience:
1
Security
Prevent breaches with firewalls, encryption, and access controls.
2
Availability
Keep systems running with redundancy, disaster recovery, and uptime monitoring.
3
Processing integrity
Ensure accurate and authorized data handling.
4
Confidentiality
Protect sensitive data with encryption and restricted access.
5
Privacy
Manage personal data in line with privacy regulations and organizational policies.
The software escrow — SOC 2 connection
Software escrow directly supports SOC 2 compliance by securing your critical software assets and demonstrating robust risk management when vendor relationships fail.
SOC 2 risk
Essential software access gets lost during vendor failures
Third-party risk controls fail during compliance audits
Continuity plans provide no proof of workable recovery processes
Software escrow solution
Stores critical software assets with legal access rights
Verifies materials contain necessary components
Automatically maintains current versions of all deposits
Compliance outcome
Demonstrates effective third-party risk management
Provides evidence of vendor contingency planning
Meets availability and continuity criteria
When SOC 2 auditors challenge your vendor dependency management, software escrow offers verified assets instead of documentation promises. Without it, you can’t prove you have the technical components needed for actual business continuity.
Let us help you with SOC 2 compliance
Codekeeper combines comprehensive knowledge of AICPA trust service criteria with advanced software protection expertise to deliver solutions specifically designed for service organizations managing SOC 2 compliance controls.
We see the challenges you face:
Complex third-party risk management requirements with extensive documentation needs
SOC 2 audit timelines with significant business consequences for delays or failures
Uncertainty about demonstrating adequate vendor failure contingency planning
Ongoing reliance on critical software vendors without backup access plans
We've secured critical software assets for thousands of service organizations globally. We can strengthen your SOC 2 compliance posture, too.

Codekeeper's complete solutions for SOC 2 requirements
Our escrow solutions address SOC 2's third-party risk management and business continuity requirements while protecting your most critical software dependencies.
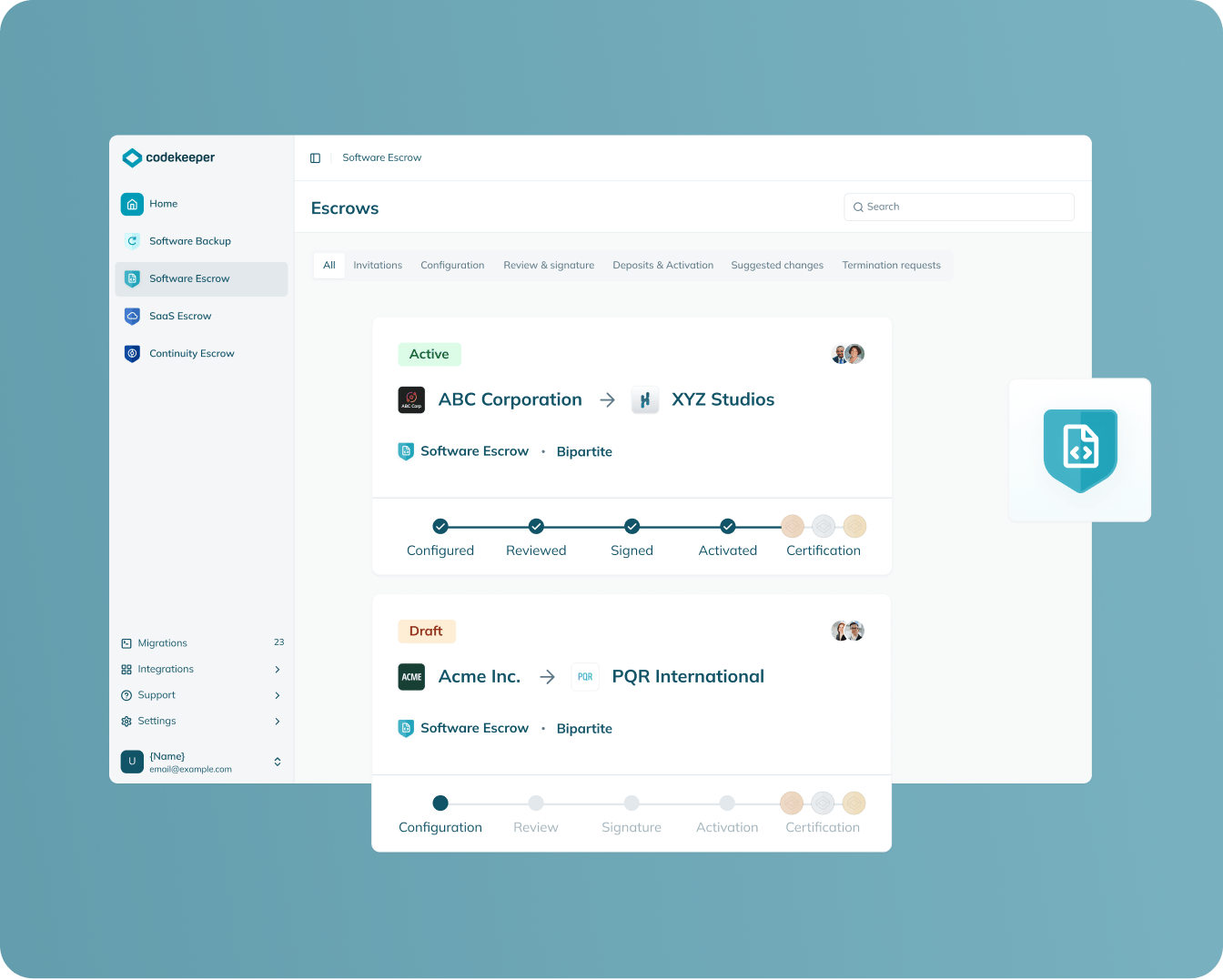
Software Escrow
Protection scope: On-premises software and applications
Safeguards locally-installed software through secure code repositories and legal agreements that guarantee access to source materials during vendor disruptions.
Documents third-party software risk controls
Establishes verifiable recovery capabilities
Creates vendor failure contingency plans
Provides audit-ready evidence of third-party risk mitigation
Learn more
SAAS escrow
Protection scope: Cloud-based applications and services
Captures complete SaaS environments, including source code, databases, and configurations, to enable independent operation when cloud providers become unavailable.
Extends third-party risk identification to cloud service dependencies
Enables recovery of web-based critical operations
Addresses modern SaaS vendor monitoring obligations
Delivers documented recovery procedures
Learn more

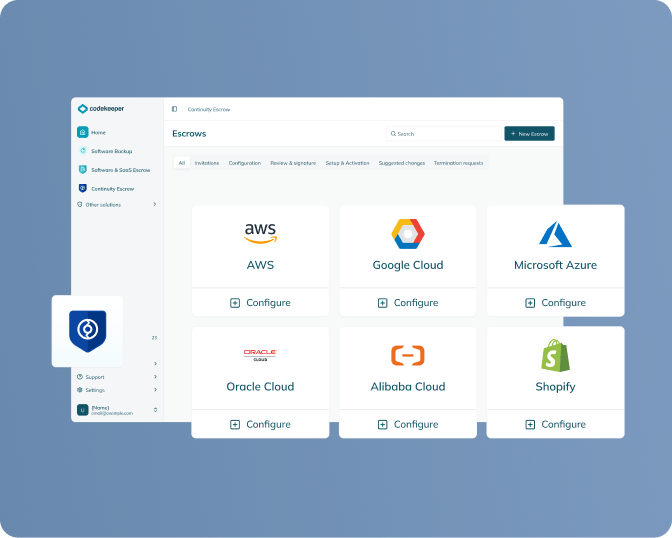
Continuity escrow
Protection scope: Supporting infrastructure and services
Continues payments to essential service providers to ensure operational continuity during vendor financial difficulties.
Manages cascading third-party risks
Prevents availability control failures during vendor payment disruptions
Creates operational continuity documentation
Supports comprehensive vendor compliance monitoring obligations
Learn more
Verification
Protection scope: All escrowed materials
Rigorously tests deposited materials through independent validation processes to confirm functionality and completeness.
Confirms deposited materials contain all necessary components for recovery
Identifies missing elements or technical issues before emergencies occur
Validates realistic timelines for system restoration procedures
Generates Software Resilience Certificates for compliance audit records
Learn more

Build SOC 2 compliance in 4 simple steps
SOC 2 requires you to demonstrate effective third-party risk management and vendor continuity planning. Here's how to establish these critical controls:
1. Schedule your compliance assessment
We'll analyze your vendor dependencies and determine which software assets require escrow protection for third-party risk management requirements.
2. Select your escrow strategy
Pick standard escrow protection or include verification services for comprehensive SOC 2 evidence of recovery capabilities and control effectiveness.
3. We manage the entire implementation process
Our specialists coordinate vendor agreements, establish legal frameworks, and configure automated deposits — minimal involvement needed from your team.
4. Receive your compliance documentation
Get verified proof that your vendor failure contingencies meet SOC 2 standards, including Software Resilience Certificates for audit records.
One assessment. One solution. Complete software risk management for SOC 2 compliance.
Book a free demo
Codekeeper takes the complexity out of compliance
Over the years, we've helped thousands of service organizations protect their critical software without drowning in SOC 2 technical details. Our solutions make third-party risk management requirements straightforward and manageable.
The cost of weak vendor risk management
Operating without robust third-party risk controls and software failure contingencies exposes your organization to cascading business risks:
Enterprise market lockout
Without demonstrable vendor risk management, you're automatically disqualified from enterprise opportunities.
Catastrophic service disruptions
When critical vendors fail without backup plans, operations stop instantly, revenue halts, and your reputation suffers.
Competitive elimination from key sectors
Rivals with stronger vendor frameworks capture market share while you're explaining why your systems lack basic continuity safeguards.
Compliance failures across multiple frameworks
Weak vendor controls cause audit failures beyond SOC 2, threatening ISO certifications, industry standards, and regulatory compliance.
Client exodus during vendor crises
Customers leave when vendor failures disrupt stability, taking renewals and revenue with them.
Don't let incomplete software risk planning delay your SOC 2 timeline. Build audit-ready third-party controls now.
E-BOOK
The CRA: Your Complete Compliance Guide
Fill in the form below to get expert guidance on meeting Europe's cybersecurity requirements for connected products.

*E-book available only in English
Get your free CRA compliance guide
How you benefit from SOC 2 compliance
Access enterprise markets with confidence
Your third-party risk management documentation becomes a competitive advantage, qualifying you for deals that non-compliant rivals can't even bid on.
Build unshakeable operational resilience
Robust vendor controls and software escrow protections ensure your operations survive when critical suppliers fail.
Strengthen client relationships and retention
SOC 2 certification shows customers that their data and operations are protected by institutional-grade risk management.
Develop controls that satisfy multiple frameworks
SOC 2 risk management builds the foundation for ISO certifications, industry standards, and regulatory compliance across your business.

Position your organization for SOC 2 success
Our compliance specialists will show you exactly how our software resilience solutions address SOC 2's third-party risk management requirements while protecting your operations from vendor disruption.
Custom assessment of your specific software risk management needs
Clear explanation of how software escrow supports SOC 2 compliance
No technical complexity or overwhelming compliance jargon
Actionable implementation steps you can begin immediately
Frequently asked questions
What is a SOC level 2?
SOC 2 is a security audit that proves to clients you can protect their data. An independent auditor examines your systems and processes, then issues a report showing whether you meet security standards. There are two types: Type 1 reports check if your security controls exist. Type 2 reports prove those controls work by reviewing them over several months.
What are the five principles of SOC 2?
The five trust services criteria of SOC 2 are Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Is SOC 2 the same as ISO 27001?
No. SOC 2 is for service organizations to prove data protection to clients, while ISO 27001 is an enterprise-wide information security management standard.
Why is software escrow important for SOC 2 compliance?
Software escrow addresses specific SOC 2 control requirements like CC3.2 (third-party risk assessment) and A1.2 (business continuity planning). When auditors ask how you'll maintain operations if vendors fail, escrow provides concrete evidence and documented contingency plans rather than theoretical responses.
Can Codekeeper help with SOC 2 readiness?
Yes. Codekeeper offers verified software escrow solutions that meet SOC 2 control requirements and produce audit-ready documentation. Our Software Resilience Certificates serve as trusted proof that auditors accept for third-party risk management and business continuity.


