Software Verification
Get your software resilience certified
We run software verification — automated and human reviews — to check your software's reliability and hand you certificates that meet every regulatory and client requirement.

Source code in escrow is just stored potential. Certification confirms its practical value. Together, they complete your protection strategy — for guaranteed continuity and regulatory compliance.
Why risk your reputation — or revenue — on unverified assets?
Depositor diligence
Can you trust the depositor secured all assets for uninterrupted service?
Comprehensiveness check
Are you sure every essential component is verified and present?
Recovery readiness
Will your deposit hold up to restore operations seamlessly?
Verified resilience
Can you prove that you can keep your software running no matter what?
We understand the weight of risk and regulatory pressure
We know how demands for software resilience weigh heavy on you. Over the last decade, our experts have helped thousands of teams secure their assets. Let us help you, too.
Have questions about software verification? We can help.
Not sure what software verification is? Wondering about how verification can help you build stronger software resilience or how it fits into your development cycle? Our experts are ready to explain what you need to know and answer your specific questions.
Demonstrate your software resilience with escrow certificates
We offer three levels of software verification — Validated, Verified, and Certified — to help you prove that your deposited assets are safe and usable. Each of these tiers also comes with an escrow certificate that shows how resilient your software is.
Validated
Automated validation that shows which assets are included in your escrow.
Best for initial peace of mind:
Onboarding new vendors/clients
Ensuring all your assets are in escrow
Free
Download free sample
Checks:
Source code deposits
Deployment config submissions
AI stack uploads
Provider details and credentials
Verified
Automated review of all escrowed materials and any updates made to them.
Best for internal quality checks:
Keeping development on track
Managing third-party vendors
Reducing project risks
From
$29
/mo
Download free sample
Checks everything under Validated, plus:
Content profiles — assets size, etc.
Development and version updates
Prompt and instruction files
Login verification tests
Certified
In-depth human analyses that give you complete assurance of continuity.
Best for meeting strict regulations and industry standards like:
ISO
DORA
NIS2
CPS 230
From
$249
/mo
Download free sample
Checks everything under Verified, plus:
Complete software build runs
Application deployment validation
Full AI stack reproducibility tests
Admin access reviews
Which verification tier is right for you?
Compare our verification features side-by-side to see exactly what each includes:
Core purpose
Validated
Shows which assets are present in escrow
Verified
Reviews all escrowed materials and updates
Certified
Tests whether the software can be recovered through expert human review
Software Resilience Certificate
Validated
To meet basic software resilience requirements for new vendor relationships.
Verified
Best for managing software project risks and ensuring development stays on track.
Certified
Ideal for CRA, DORA, NIS2, CPS 230, FFIEC, KRITIS, ISO 27001, SOC 2, or ESMA.
Ongoing monitoring
Validated
Verified
Monthly activity reports
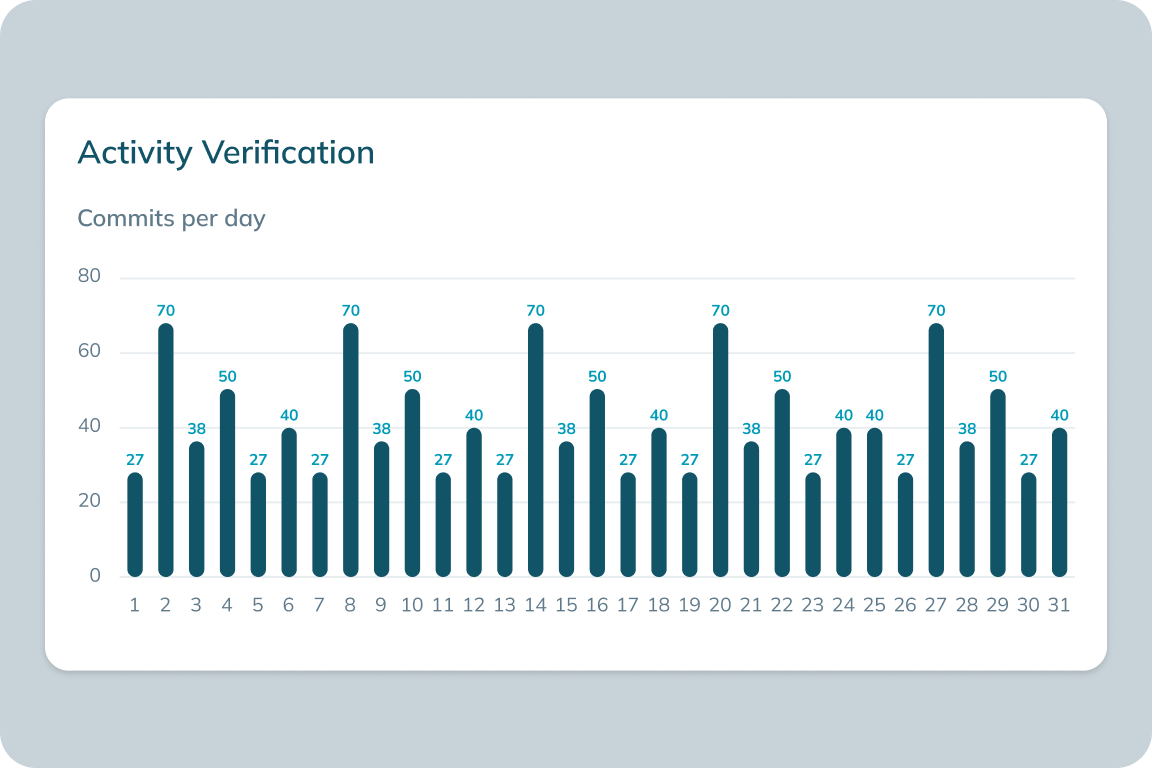
Shows recent code changes, account activity, credential status, and which services are still accessible.
Certified
Monthly reports + annual expert review
Monthly reports showing asset status and activity, plus detailed yearly report from experts confirming everything is ready for recovery.
Resilience assurance
Validated
Your software files exist and are accessible
Verified
Your software appears complete and legitimate
Certified
Your software can be built during recovery
Validated
Verified
Certified
Review type
Automated component inventory
Automated checks available for supported platforms only
Automated content + activity analysis
Expert human review
Volume discounts available for multiple expert reviews per year
Core checks
Confirms all files are securely stored
Software, SaaS, AI, and Continuity Escrow Verification
Analyzes repository size and contents
Software and SaaS Escrow Verification
Tracks code and AI configuration changes and updates
Software, SaaS, and AI Escrow Verification
Reviews component size and contents across your AI stack
AI Escrow Verification
Checks admin access via escrowed credentials
Continuity Escrow Verification
Shows your code compiles and runs without errors
Software and SaaS Escrow Verification
Tests whether your AI stack rebuilds, loads, executes, and operates as expected
AI Escrow Verification
Certifies that admin access works
Continuity Escrow Verification
Validated
Verified
Certified
Core purpose
Shows which assets are present in escrow
Reviews all escrowed materials and updates
Tests whether the software can be recovered through expert human review
Software Resilience Certificate
To meet basic software resilience requirements for new vendor relationships.
Best for managing software project risks and ensuring development stays on track.
Ideal for CRA, DORA, NIS2, CPS 230, FFIEC, KRITIS, ISO 27001, SOC 2, or ESMA.
Ongoing monitoring
Monthly activity reports
Shows recent code changes, account activity, credential status, and which services are still accessible.
Monthly reports + annual expert review
Monthly reports showing asset status and activity, plus detailed yearly report from experts confirming everything is ready for recovery.
Resilience assurance
Your software files exist and are accessible
Your software appears complete and legitimate
Your software can be built during recovery
Review type
Automated component inventory
Automated checks available for supported platforms only
Automated content + activity analysis
Expert human review
Volume discounts available for multiple expert reviews per year
Core checks
Confirms all files are securely stored
Software, SaaS, AI, and Continuity Escrow Verification
Analyzes repository size and contents
Software and SaaS Escrow Verification
Tracks code and AI configuration changes and updates
Software, SaaS, and AI Escrow Verification
Reviews component size and contents across your AI stack
AI Escrow Verification
Checks admin access via escrowed credentials
Continuity Escrow Verification
Shows your code compiles and runs without errors
Software and SaaS Escrow Verification
Tests whether your AI stack rebuilds, loads, executes, and operates as expected
AI Escrow Verification
Certifies that admin access works
Continuity Escrow Verification
We can verify your outside-the-box
software, too
We understand that many organizations have unique setups that don't fit neatly into standard solutions. Our custom verification service adapts to your specific requirements and focuses on the critical vulnerabilities and edge cases that generic tests often miss.
Custom Verification
Tailored solutions built for your specific software architecture and goals
Complete verification of your entire software infrastructure
Flexible environment configuration to match your production settings
Comprehensive feature testing based on your actual usage scenarios
Let us know what you need, and we'll create a verification approach that gives you maximum confidence in your software's reliability and performance.

How software verification works
1. Upload your assets — code, configs, credentials — to Codekeeper's secure vault.
2. We run automated checks and expert reviews based on your tier.
3. Receive certificates and reports proving your software's resilience.
4. Pass audits, secure clients, and guarantee uptime — it's that easy.
We provide concierge support at every step.
Book a free demo
Certify your software continuity
Integrate your Codekeeper escrow solution with our verification services to earn trusted certificates that show your systems meet all software resilience requirements.
Document compliance to avoid interruptions
Verification compiles reports and certificates by analyzing your assets against development and maintenance rules — like ensuring code is updated quarterly. You get a breakdown of what's compliant and what needs work, submitted automatically or reviewed by experts. This keeps regulators satisfied and your software available.

Track development activity for alignment
Verification monitors changes in your software, such as new code commits or config edits, by comparing your deposit to your active repository or storage bucket. It flags what's been updated and when, so your escrow stays current.
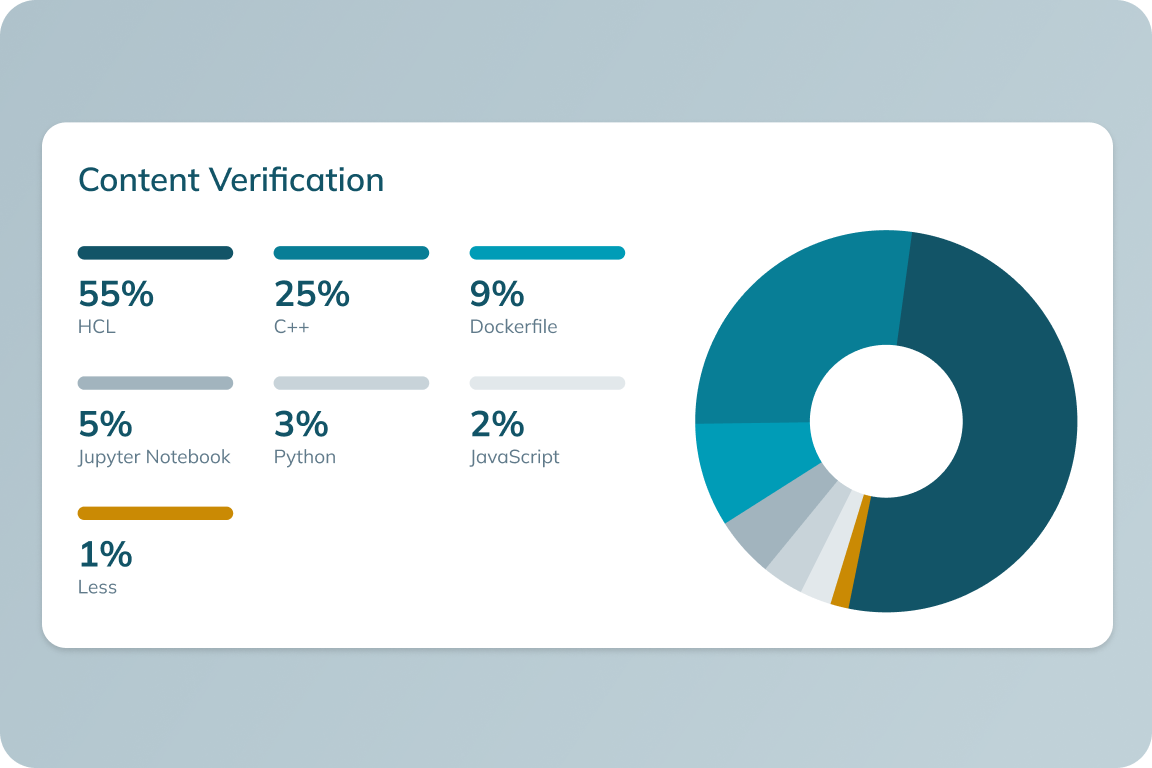
Verify deposit contents for reliability
Verification scans your escrow deposits — source code, databases, configs — and logs details like file sizes, who worked on them, and recent updates. Automated tools list what's in your vault, while additional human builds and reviews check if it matches your live software. This ensures you have everything needed to stay online.
E-BOOK
Software Verification 101
Fill in the form below to learn how verification keeps your software running.

*E-book available only in English
Get your free introduction to software verification
Don't let unverified software break your business
Software failure triggers outages, costs you revenue, and drives users away.
Regulatory fines pile up fast when audits expose gaps in your deposit.
Downtime always strikes at the worst moment — you shouldn't risk it.
With Codekeeper, verification is simple — your software stays on, and the pressure stays off.

Software Verification
Don't wait for a failure to show you're unprepared
Secure continuity the easy way. Our source code verification services deliver proof of continuity right to your dashboard.
Eliminate software risks completely.
Grow client trust with detailed reports.
Earn certificates to prove your software resilience.
Frequently asked questions
What is software verification?
Software verification evaluates escrow deposits, like source code and configurations, to ensure they're secure, complete, and functional. It confirms the assets can support business continuity if released and offers certificates for compliance and trust.
What is the difference between software verification and validation?
Verification tests if the deposit is usable (e.g., code runs), while validation checks if all required assets are included, focusing on presence over functionality.
What are the three verification levels?
The three levels of verification are Validated, Verified, and Certified. The Validated level offers a free check to ensure all agreed-upon assets, like source code and documentation, are present in the escrow deposit. The Verified level uses automated reviews to verify quality and alignment with production needs. The Certified level provides a full software build to prove the deposit is fully operational.
What can be held in escrow?
An escrow account can hold a variety of essential software-related materials, including the source code, system configurations, detailed technical documentation, and other critical digital assets required to ensure that software can be recovered if needed.

