We protect your software so it never fails you
Audit-ready software escrows, backups, verification, and continuity services for on-premises systems, SaaS applications, and AI tools.
- Survive system failures
- Avoid operational downtime
- Ward off non-compliance penalties
Join 3 500+ teams who've already protected their software
Right now, your software is exposed to preventable risks
Anything that keeps your software offline, underperforming, or stuck in development is a business risk. And there’s plenty of them.
Failure
Whether you're building software or using it, you rely on critical vendors — and their failure cascades directly to you.
Vendor shutdown
Bankruptcy, insolvency, business closure, or acquisition leaves you without your software.
Geopolitical disruptions
Overnight tariffs, sanctions, or export bans instantly cut off your access or increase costs dramatically.
Downstream provider outages
Vendor, infrastructure, and provider dependencies — failure at any level takes down your systems too.
At least two in 10 vendors will fail within three years.
Most companies rely on 200+ vendors to operate.
That means permanent loss of 40+ systems your business depends on.


Attacks
Attackers are already in your systems. You just haven't detected them yet.
Ransomware attacks
Criminals lock you out of production systems, development environments, and backups simultaneously.
Supply chain infiltration
Hackers poison one library, which infects everything connected to it throughout your infrastructure.
Backup destruction
Attackers target and corrupt disaster recovery first so you have no way back.
Nearly 2 000 attacks hit organizations every week.
Only one has to get through
to knock out your systems, backups, and any chance of recovery before you can even react.
Non-compliance
Regulations expand and change constantly. So, meeting today's requirements doesn't guarantee tomorrow's compliance.
Market disqualification
Without compliance certifications, you've disqualified yourself from enterprise deals before negotiations start.
Regulatory fines
Non-compliance penalties reach €10M or 2% of revenue under EU regulations.
Executive criminal liability
Compliance failures lead to personal fines, management bans, and criminal prosecution for board members.
Missing compliance certifications costs companies $4.2 million in lost deals plus $1.8 million in delayed revenue.
You're hemorrhaging millions while competitors close contracts you’re excluded from.


Broken
If you're not testing your software, chances are it carries invisible defects waiting to crash your systems.
Unvetted AI code
AI-generated code contains logic errors, hallucinations, and vulnerabilities no one verified before production.
Corrupted updates
Software updates inject bugs that corrupt production data and break critical functionality.
Accumulating technical debt
Legacy code piles up faster than you can fix it, making systems impossible to maintain.
66% of companies experience major outages within 12 months of deploying untested code.
When the outage hits, they can't fix it — they don't know what broke, and they don't have the code to repair it.
CASE STUDY
Everyone’s at risk — there are no exceptions
One vendor carries a 42% chance of failure, with five vendors, that jumps to 90%. By 10, you’re at 99%.
When Jaguar Land Rover's vendor systems were compromised in 2025, three factories stayed offline for weeks, costing £50 million per week.


Are you sure you want to leave your software unprotected?
If you can't restore your systems within hours of a disaster event, your business won't survive the downtime. For peace of mind, get Codekeeper Software Resilience today.
Codekeeper protects thousands of companies’ software across all industries
We know you can’t afford to waste time with recovery. That’s why Codekeeper makes sure no single mistake, change, or incident can erase your software’s foundations or the blueprints to rebuild it.
We keep extra copies of your code, data, and documents in secure vaults so you don't lose them when your systems fail.
We secure an encrypted version of your software that attacks can't touch.
We hold certified records that prove these backups exist and work.
We check for weaknesses so your software doesn't transform into something unreliable.
10+ years
guarding critical software
$5,000+
reduction in legal fees per client
40+ hours
saved in DevOps work
Learn more about Codekeeper


We're ISO 27001 certified
We sought ISO 27001 certification to verify that our security practices meet international standards. This rigorous process helps us better secure your systems.
Open our Trust Center
From at-risk to resilient in 3 simple steps
1. Book a consultation with our experts
A 30-minute call where you talk through your dependencies with someone who understands software risk.
2. Set up your software protection
You select your plan, connect your systems, and invite your team — everything syncs automatically.
3. Get verified and receive your certificate
We test your materials, confirm they work, and deliver your Software Resilience Certificate ready to share with auditors and clients.
We provide concierge support at every step.
Book a demo
Multi-level protection to help you build software resilience fast
Codekeeper helps you build complete software resilience by securing everything needed to keep your critical software working, from source code and credentials to full redeployment plans. It's not just code storage; it's total software protection.
Recovery
Software Backup
Automatic daily backups of your internal systems with unlimited storage.
Learn more

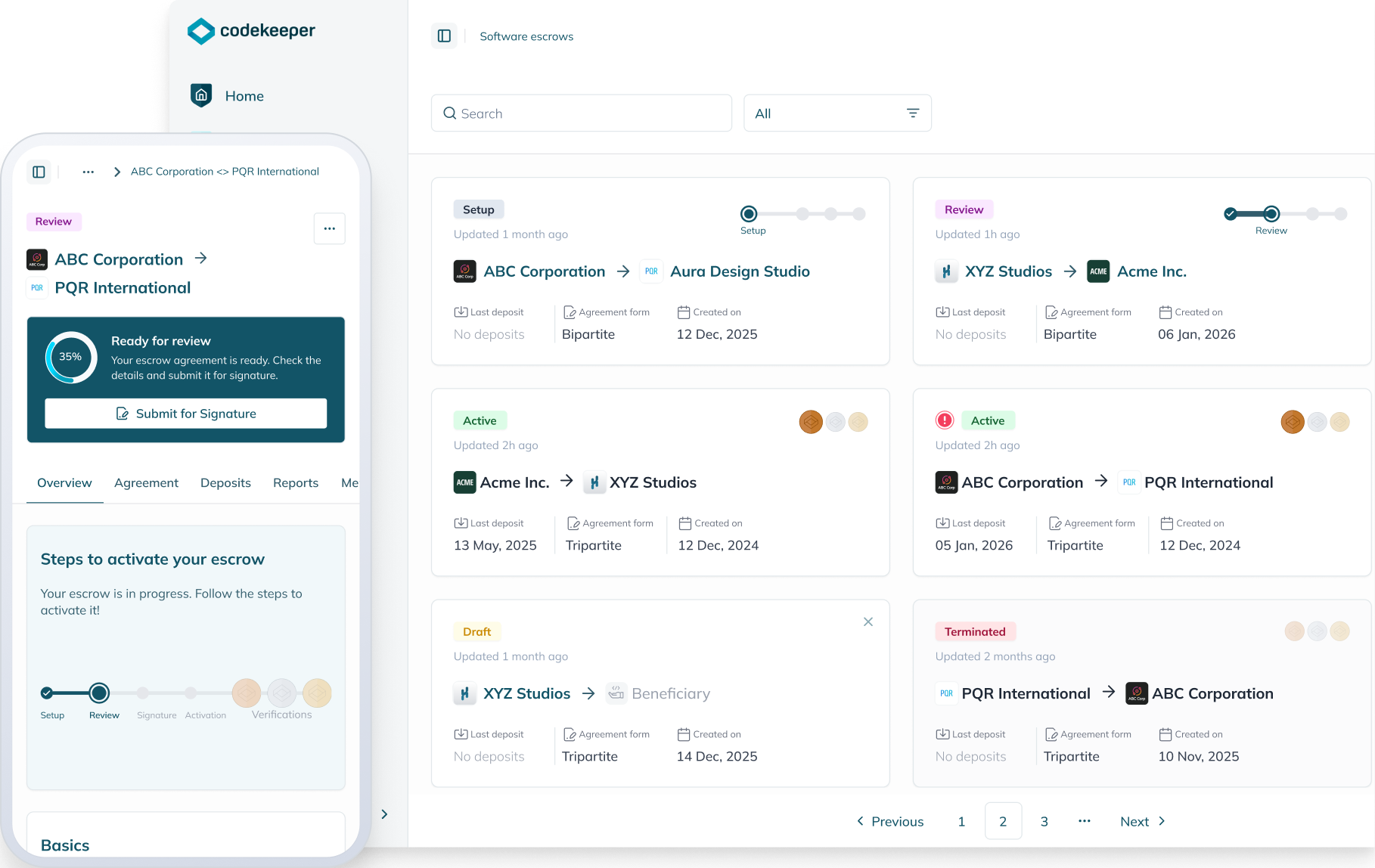
Software Escrow
Secure vault for on-premises software source code, data, and documentation.
Learn more

SaaS Escrow
Preserved access to cloud application components and deployment assets.
Learn more

AI Escrow
Complete protection for your AI stack including models, prompts, and workflows.
Learn more

Assurance
Validated
Confirmation that all essential materials are in your escrow deposits.
Learn more

Verified
Automated checks on deposit activity, file integrity, and content completeness.
Learn more


Certified
Technical testing that proves your materials are recovery-ready and functional.
Learn more


Each verification level comes with a Software Resilience Certificate you can share with auditors, clients, and stakeholders.

Validated
Confirmation that all essential materials are in your escrow deposits.
Learn more

Verified
Automated checks on deposit activity, file integrity, and content completeness.
Learn more


Certified
Technical testing that proves your materials are recovery-ready and functional.
Learn more


Each verification level comes with a Software Resilience Certificate you can share with auditors, clients, and stakeholders.

Each verification level comes with a Software Resilience Certificate you can share with auditors, clients, and stakeholders.

Better protection, better value, better experience
We've rethought escrow from the ground up to give you more flexibility, more features, and better value than traditional providers.
Unlimited everything, no surprises
Unlimited automated deposits that sync daily. No per-deposit fees. No storage caps. No surprise charges.
More features, lower costs
Start with free software validation and online agreement management. Scale up to recovery support and advanced verification as your needs change.
Flexible plans that fit your business
Choose monthly or annual plans (most providers only offer annual). And easily add multiple beneficiaries or vendors to your plan as you grow.
We sync with your systems
The Codekeeper app supports 50+ integrations to convert fragmented processes into a cohesive continuity flow. Link your systems once for automatic daily syncs, up-to-date backups, and current escrow deposits.
View all integrations



If you can't guarantee recovery when software fails, everything is at risk.
Your operations. Your compliance. Your reputation.
With Codekeeper Software Resilience, you get protection that covers it all.
With Codekeeper Software Resilience, you get protection that covers it all.
When systems go down, you have source code access.
When auditors ask, you have certified proof.
When clients demand assurance, you have documentation ready.
These companies’ systems are protected, compliant, and resilient
They made the decision. They built their resilience. They have peace of mind. You can too.
“We’ve had a great experience with CodeKeeper. The setup process was smooth, and the team made everything very straightforward. Knowing our critical software assets are securely protected gives us real peace of mind. Their support has been responsive and professional, and the overall service has been reliable and easy to work with. Highly recommended.”
Jordan Adler
“We worked with Codekeeper as our escrow provider for major enterprise deployments and found them to be extremely professional, responsive, and flexible throughout.
I'd highly recommend Codekeeper. They clearly understand the realities of working with growing tech businesses and enterprise customers alike.”
I'd highly recommend Codekeeper. They clearly understand the realities of working with growing tech businesses and enterprise customers alike.”
Ross Kilshaw
I found Codekeeper's solution excellent for what I need. I scheduled a demo to better understand the possibilities. Very easy! It was a clear and straightforward meeting, focused exactly on what I needed. Excellent service!
Thiago Mendes
Ready to protect your software?
If you're worried your software is at risk, talk to our experts today about implementing software resilience. It's the right call to make.
- No-pressure consultation to explore your options
- Guided implementation with expert support
- Fast certification with immediate proof

E-BOOK
New to software escrow?
Download our free guide to learn how escrow works, why companies use it, and how to implement it for your business.

*E-book available only in English
Get your free introduction to software escrow
Frequently asked questions
Why trust Codekeeper?
Our team of experts has spent the last decade researching and developing new ways to mitigate cyber risks. We were the first to introduce automatic deposit syncing, and we continue to innovate to keep your critical data and applications secure, up-to-date, and always available.
What industries benefit most from Codekeeper's solutions?
Codekeeper's suite of software resilience solutions benefits any business reliant on digital assets, including those in finance, healthcare, manufacturing, e-commerce, logistics, and the public sector.
What is software escrow?
Software escrow is a legal arrangement that protects licensed software users by ensuring continuous access to the software's source code and other critical materials. In a software escrow agreement, the software developer or vendor deposits a copy of the source code, documentation, and other essential components with a trusted third-party escrow agent, such as Codekeeper. This agent securely stores and manages these materials on behalf of the software provider and the beneficiary.
Why do companies use escrow?
Companies use software escrow to mitigate risks and ensure business continuity. An escrow agreement guarantees the licensee can maintain, update, and use the critical software without disruption, even if the original vendor is no longer available to provide support.
How does software resilience escrow protect your business?
Software resilience solutions protect your business by minimizing downtime, saving critical data, and guaranteeing quick restoration of essential systems when unexpected disruptions occur. A comprehensive plan can prevent revenue loss, mitigate legal and regulatory repercussions, and maintain your business's trust and operational excellence.






